Recon quality decides how useful the rest of a penetration test will be. Weak recon usually creates two bad outcomes: missed attack surface and noisy findings that waste engineering time. Strong recon gives you clean asset visibility, ownership confidence, and better test depth when web, API, and cloud validation starts.
This workflow is written for authorized engagements only: internal assessments, approved client scopes, and controlled labs.
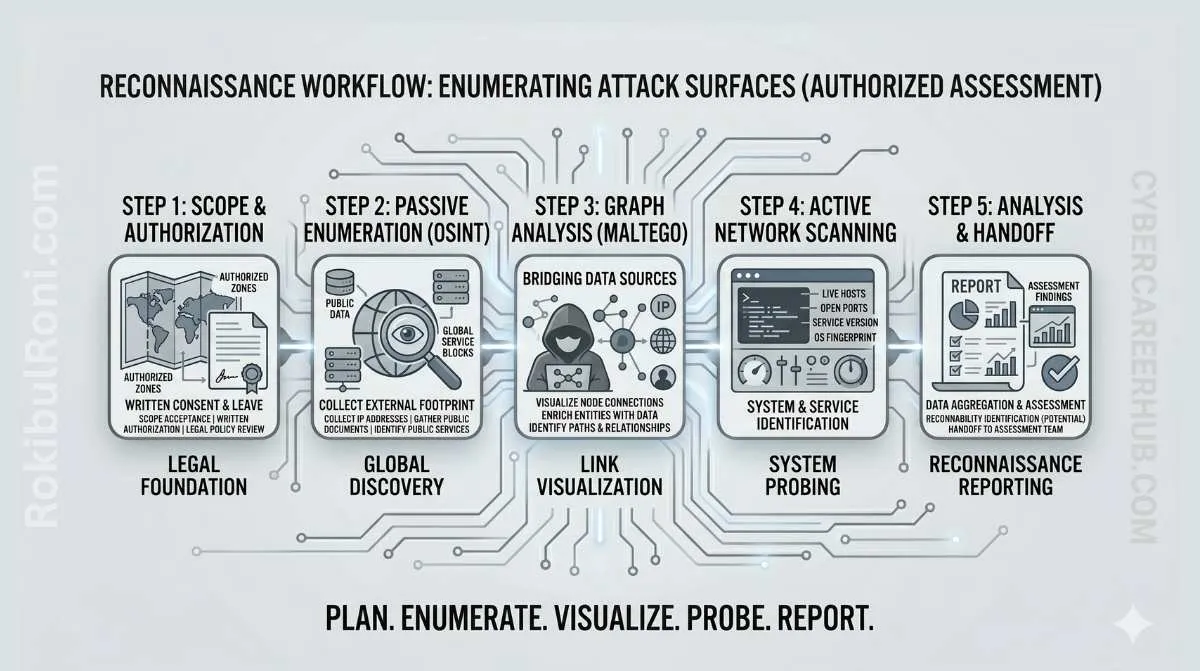
Recon workflow for authorized security assessments
Treat recon as a phased evidence pipeline, not a one-shot scan.
Phase model: passive, semi-passive, active validation
| Phase | What You Do | Typical Data Sources | Operational Risk | Main Goal |
|---|---|---|---|---|
| Passive Recon | Collect externally visible information without direct probing | Certificate transparency logs, WHOIS/RDAP, DNS records, public documentation | Very low | Build initial asset candidates |
| Semi-Passive Enrichment | Enrich candidates with external telemetry and relationship mapping | Shodan, search engines, passive DNS context, historical certs | Low | Add context and risk signals |
| Authorized Active Validation | Validate candidate assets and service posture directly in scope | Nmap, browser checks, DNS resolution checks | Controlled by scope | Confirm what is actually live and owned |
If scope allows only passive recon, stop there and report uncertainty explicitly. Do not drift into active probing without approval.
Scope boundaries and rules of engagement
Recon errors usually start as scope errors. Lock boundaries before tooling.
Scope control checklist
- Approved target domains, subdomains, and IP ranges
- Explicit exclusions (partners, third-party SaaS, CDN-owned infrastructure)
- Approved active methods (service discovery, version checks, timing limits)
- Allowed test windows and escalation contacts
- Data handling constraints (retention, redaction, sharing)
- Rules for cloud-hosted and multi-tenant infrastructure
- Stop conditions for instability or legal ambiguity
Rules-of-engagement table
| Control | Required Clarification | Why It Protects the Engagement |
|---|---|---|
| Ownership Verification | Who owns each domain/IP/system in scope | Prevents scanning unrelated organizations |
| Method Approval | Which active checks are permitted | Keeps validation safe and contract-aligned |
| Time Boundaries | Testing windows and blackout periods | Reduces production disruption risk |
| Escalation Path | Security + infrastructure contacts | Speeds handling of alerts or incidents |
| Data Governance | Evidence storage, retention, and masking | Keeps recon artifacts compliant |
Stage 1: Asset intake and source-of-truth setup
Start from official asset ownership, not tool output.
Intake inputs
- CMDB or service registry exports
- Known domains, brands, and business units
- Cloud account/project/subscription naming patterns
- Existing DNS zone records and delegated subzones
- Historical pentest and vulnerability reports
Working inventory fields
- Asset identifier (domain, host, IP, app name)
- Claimed owner team
- Business criticality
- Exposure type (public/internal/hybrid)
- Confidence score (initially low)
- Validation status (unvalidated/validated/rejected)
Keep this inventory in a spreadsheet or ticketed tracker so every recon decision is auditable.
Stage 2: Domain and subdomain discovery
Use multiple discovery paths, then deduplicate aggressively.
Practical approach
- Enumerate root domains from scope documents.
- Collect subdomain candidates from approved discovery tools and CT logs.
- Normalize naming patterns (remove duplicates, typos, stale aliases).
- Resolve DNS and capture A/AAAA/CNAME status.
- Flag unresolved or parked records for separate review.
Recommended tooling mix
Amassfor broad discovery and correlationSubfinderfor fast passive candidate gatheringcrt.shfor certificate-derived hostname discovery- DNS utilities for resolution and record typing
Do not treat every discovered hostname as owned or active. Discovery produces leads, not confirmed assets.
Stage 3: Certificate and DNS review
Certificate history and DNS context often reveal forgotten exposure.
What to review in certificate data
- SAN entries linked to current and legacy services
- Unexpected environment labels (dev, old, temp, backup)
- Issuance patterns tied to unknown teams or domains
What to review in DNS data
- Long-lived records pointing to retired infrastructure
- CNAME chains ending in third-party managed services
- Dangling references and stale delegations
- Split-brain behavior between public and internal DNS views
DNS/certificate signal table
| Signal | Possible Meaning | Validation Action |
|---|---|---|
| Certificate includes old subdomain names | Legacy service path may still exist | Resolve and check ownership status |
| CNAME to decommissioned platform | Orphaned routing or takeover risk | Confirm deprovisioning and update DNS |
| Multiple records with inconsistent TTL behavior | Change drift or unmanaged edits | Review with DNS owner and change logs |
| Unresolved hostname still in docs | Documentation drift | Mark as stale and verify business impact |
Stage 4: Shodan enrichment and exposure context
Shodan is enrichment, not ground truth.
Enrichment objectives
- Identify likely internet-facing services tied to candidate assets
- Capture observed service banners and protocol metadata
- Prioritize systems for authorized active validation
Safe usage notes
- Record timestamp for every Shodan observation
- Tag each result as unverified until ownership is confirmed
- Avoid direct severity claims based only on banner data
Prioritization signals from enrichment
- Public admin interfaces tied to business apps
- Exposed management protocols requiring review
- Legacy service stacks with known patch lag patterns
- High-traffic public endpoints with weak control indicators
Stage 5: Maltego graphing for ownership and relationship clarity
Maltego helps answer: “Which exposed thing belongs to whom, and how does it connect?”
Graphing workflow
- Seed graph with approved root domains and known organizations.
- Add discovered hostnames, certificate entities, and IP relationships.
- Group by business unit, environment, and service owner.
- Mark uncertain nodes for manual validation.
- Export graph snapshots with date/time and analyst notes.
What graphing improves
- Ownership ambiguity reduction
- Third-party boundary visibility
- Faster scoping of downstream validation tasks
- Cleaner reporting narrative for stakeholders
Stage 6: Technology fingerprinting and service hypotheses
Before active checks, build hypotheses from passive and enriched data.
Hypothesis examples
- “This hostname likely fronts an API gateway for customer onboarding.”
- “This IP appears to host legacy admin service paths.”
- “This domain likely routes through shared CDN edge with separate origin controls.”
Keep hypotheses explicit so active validation can confirm or reject them quickly.
Stage 7: Authorized Nmap validation
This is where assumptions meet reality. Keep scans narrow, controlled, and logged.
Validation priorities
- Confirm host liveness for scoped assets
- Confirm exposed service ports required for business use
- Validate protocol/service identification at a safe level
- Detect unexpected exposed services for owner review
Operational safeguards
- Use approved target lists only
- Use conservative timing and rate settings
- Track command profile and scan window in notes
- Stop immediately on instability signals
Validation outcome table
| Validation Result | Interpretation | Next Step |
|---|---|---|
| Expected service exposed | Baseline appears accurate | Move to application/API testing prep |
| Unexpected service exposed | Potential attack surface expansion | Confirm ownership and risk review |
| Host unreachable but documented as active | Possible stale inventory or routing issue | Verify with infra team |
| Service fingerprint uncertain | Data quality gap | Re-check with alternate approved method |
Recon evidence table for reporting
Use this table format during recon execution so output is immediately report-ready.
| Source | Asset | Confidence | Risk Signal | Next Action |
|---|---|---|---|---|
CT logs (crt.sh) | api.example.com | Medium | Seen in recent certs, ownership not yet confirmed | Validate DNS + owner mapping |
| Passive subdomain discovery | admin-old.example.com | Low | Legacy naming pattern suggests forgotten service | Resolve record and verify status |
| DNS review | files.example.com CNAME chain | High | Points to third-party platform | Confirm ownership and access model |
| Shodan enrichment | Public HTTPS endpoint on scoped IP | Medium | Banner indicates legacy stack | Prioritize authorized validation |
| Maltego graph | Domain linked to unknown entity | Low | Possible third-party managed node | Escalate ownership clarification |
| Nmap active validation | Scoped host with unexpected service | High | New exposed service in approved scope | Open finding candidate and notify owner |
Avoiding false positives and stale recon noise
Recon findings become credible only after ownership and recency checks.
Common false-positive sources
- Stale DNS records that no longer map to active services
- Historical certificates for retired services
- Shared hosting/CDN artifacts from unrelated tenants
- Shodan observations older than current infrastructure state
- Third-party service endpoints mistaken as first-party assets
False-positive reduction checklist
- Confirm current DNS resolution at capture time
- Compare observed assets with internal owner records
- Validate timestamp recency across external sources
- Require two-source confirmation before high-confidence labeling
- Mark uncertain ownership explicitly in evidence notes
How recon output feeds downstream security work
Strong recon directly improves the quality of web/API testing, vulnerability management, and red team planning.
Web and API testing readiness
- Cleaner endpoint prioritization for high-value attack surface
- Better role/environment mapping before test execution
- Reduced time wasted on irrelevant or dead targets
Vulnerability management alignment
- Clear asset ownership for remediation routing
- Better severity context through exposure + business mapping
- Faster triage because evidence is structured and timestamped
Red team and adversary simulation support
- Better understanding of public-facing trust boundaries
- Clear entry-point hypotheses for approved scenarios
- Improved blue-team coordination with known exposure map
Common reconnaissance mistakes in real engagements
- Scanning outside scope because ownership was assumed, not verified
- Trusting Shodan output as definitive without active confirmation
- Ignoring cloud and DNS context behind a simple hostname list
- Mixing third-party assets into first-party risk statements
- Running active validation before rules-of-engagement are finalized
- Failing to retain evidence timestamps and analyst decision notes
Repeatable recon checklist for each assessment cycle
| Step | Deliverable | Done |
|---|---|---|
| Scope + ROE confirmed | Approved target and method boundaries | ☐ |
| Asset intake completed | Initial inventory with ownership claims | ☐ |
| Domain/subdomain discovery finished | Candidate list with deduped hostnames | ☐ |
| Cert + DNS review completed | Relationship and stale-record notes | ☐ |
| Shodan enrichment captured | Exposure signals with timestamps | ☐ |
| Maltego graph built | Ownership and dependency map | ☐ |
| Authorized Nmap validation completed | Confirmed live service baseline | ☐ |
| Evidence table finalized | Source, confidence, risk signal, next action | ☐ |
| Handoff package delivered | Report-ready recon output for testing teams | ☐ |
When this loop is done properly, recon stops being a vague “first phase” and becomes a reusable intelligence layer that improves every assessment that follows.
Operational worksheet for recon programs
| Workstream | Owner | First Action | Validation Signal |
|---|---|---|---|
| Scope integrity | Engagement lead | Confirm ownership boundaries before discovery | Zero out-of-scope validation events |
| Asset inventory quality | Platform/security ops | Merge known assets with discovery candidates | Reduced “unknown owner” assets over time |
| Enrichment discipline | Recon analyst | Timestamp and source-tag all enrichment data | Evidence table includes confidence + recency |
| Active validation safety | Technical lead | Enforce approved methods and rate constraints | No operational disruption from validation steps |
| Reporting handoff | Security manager | Deliver source-to-action recon outputs | Testing teams accept recon pack without rework |
Recon governance checklist
- Keep ownership proof with every high-confidence asset
- Require recency checks before elevating exposure claims
- Track stale certificate and DNS artifacts separately
- Escalate unresolved ownership ambiguities early
- Record uncertainty explicitly in final handoff
Evidence and reporting pack standard
| Artifact | Minimum Content | Consumer |
|---|---|---|
| Recon inventory | Asset, source, owner, confidence, recency | Pentest + vulnerability teams |
| Exposure notes | Public signal, risk hint, verification status | Security leadership |
| Validation log | Approved scan method, target, time window, outcome | Audit + operations |
| Ownership issues list | Ambiguous assets requiring clarification | Platform/legal/security governance |
Quality controls
- Every high-risk signal must have at least two supporting sources
- Every active-validation result must include approved scope reference
- Every unresolved item must have next action and owner
90-day recon maturity plan
Days 1–30
- Normalize recon evidence formats and confidence labels
- Run one complete recon cycle on primary business domain set
- Baseline false-positive sources and ownership gaps
Days 31–60
- Improve validation logic for stale DNS/certificate drift
- Add recon output integration into pentest planning
- Track improvement in ownership verification speed
Days 61–90
- Establish recurring recon schedule tied to release cadence
- Publish recon KPIs and gap trends to stakeholders
- Formalize handoff checklist for downstream testing teams
| Metric | Why It Matters |
|---|---|
| Assets with confirmed ownership | Indicates recon governance quality |
| False-positive reduction rate | Shows data quality improvement |
| Time from discovery to validation | Reflects operational recon efficiency |
| Recon findings reused by test teams | Measures practical business value |
A recon process with clear ownership and evidence standards becomes a reusable security capability rather than an ad-hoc discovery exercise.
Recon handoff pack (what “done” should look like)
Recon is only useful when downstream teams can act on it quickly. Treat your output like a deliverable with an acceptance bar.
Minimum handoff artifacts
- Asset inventory: hostname/IP, environment guess (prod/stage), owner, confidence, recency.
- Exposure summary: what is externally reachable, why it matters, and what is unverified.
- Validation log: when/where active checks were run, the approved scope reference, and the result.
- Open questions list: ambiguous ownership, suspected third-party assets, and “needs confirmation” items.
Confidence labeling rules
| Label | Meaning | Allowed statement |
|---|---|---|
| High | Two independent sources + active confirmation (when approved) | “Confirmed asset/service” |
| Medium | Two sources but no active confirmation | “Likely asset/service” |
| Low | Single source or stale signal | “Unverified signal; requires confirmation” |
Recency standards (default)
- External datasets (Shodan/certs): treat as historical unless you can confirm freshness.
- DNS and HTTP checks: capture timestamp and resolver/location for repeatability.
- Any “high-risk” claim: require same-week confirmation or clearly mark the limit.
Operational KPIs to track (quarterly)
| KPI | Target direction | Why it matters |
|---|---|---|
| % assets with confirmed owner | Up | Reduces wasted triage and scope confusion |
| % findings reused by test teams | Up | Measures real business value of recon |
| Out-of-scope validation events | Down to zero | Measures governance maturity |
| “Stale signal” rate | Down | Measures evidence hygiene |
This makes recon output professional-grade: clear confidence, traceable evidence, and a handoff package teams can use immediately.