CI/CD pipelines are production control planes. If a workflow can push code, publish artifacts, assume cloud roles, or deploy infrastructure, it is part of your attack surface.
Hardening GitHub Actions is not about slowing delivery. It is about reducing avoidable trust risks while keeping release flow predictable.
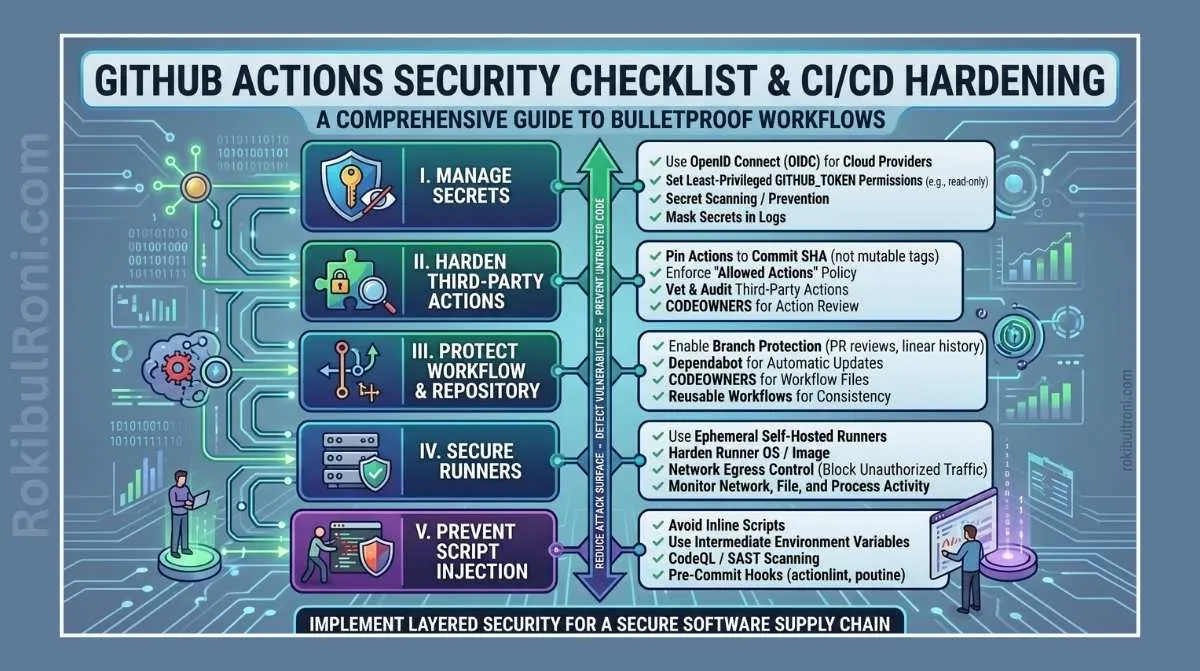
GitHub Actions security checklist
Use this as a defensive checklist and operating model for secure workflow governance.
1) Why CI/CD must be treated as high-risk infrastructure
- Pipelines can modify production code and runtime state
- Build systems often hold secrets and deployment credentials
- Workflow changes can bypass normal runtime protections
- Third-party action trust introduces external supply-chain risk
- Self-hosted runner misconfiguration can expose internal networks
If pipeline trust is weak, application security controls can be bypassed upstream.
2) Core hardening control areas
These controls should be implemented together, not in isolation.
- Workflow permissions and token minimization
- Third-party action governance and version pinning
- Branch protection and release gating
- Secrets handling and log redaction discipline
- Pull request trigger safety for untrusted contributions
- Artifact integrity and retention boundaries
- Runner isolation and lifecycle controls
- Dependency and code security checks in pipeline
3) Control table for operational use (required)
| Control | Risk Reduced | How to Review | Recommended Setting |
|---|---|---|---|
Workflow permissions block | Token overreach and unintended repo/admin operations | Inspect each workflow for explicit permissions declaration | Default to read and grant only required scopes |
Least-privilege GITHUB_TOKEN | Unauthorized write operations from compromised steps | Check job-level token usage and required API calls | Narrow permissions per job, avoid broad repo write |
| Third-party action trust | Supply-chain compromise from unvetted actions | Inventory external actions and maintain allowlist | Use trusted sources and governance approval process |
| Action version pinning | Uncontrolled behavior changes from moving tags | Search for floating refs (@main, broad tags) | Pin to immutable commit SHA where feasible |
| Branch protection rules | Direct risky changes to protected branches | Review branch settings and bypass permissions | Require PR review, status checks, and restricted force pushes |
| Environment approvals | Unreviewed deployment to sensitive targets | Validate env protection rules and reviewers | Enforce manual approval for prod/stage deployments |
| Secrets handling | Secret exposure through logs and workflow misuse | Review logs, masked values, and secret access boundaries | Scope secrets by environment and minimize availability |
| Pull request trigger safety | Untrusted code execution with privileged context | Review use of PR-related triggers and secret exposure paths | Use safer trigger patterns and strict conditions |
| Artifact exposure controls | Leakage or tampering of build outputs | Review artifact permissions, retention, and download controls | Restrict access and keep retention minimal |
| Self-hosted runner hardening | Lateral movement and persistence risk on runner hosts | Audit network access, isolation model, and cleanup behavior | Isolate runners, ephemeral where possible, minimal outbound scope |
| Dependency/code scanning | Vulnerability drift and hidden risky dependencies | Check workflow coverage and result handling | Run dependency and code scanning in PR + scheduled jobs |
| CodeQL/secret scanning coverage | Missed code and credential risk before merge | Validate enablement across key repositories | Enable by default and triage findings with ownership |
This table should live in your CI/CD governance docs and be revalidated quarterly.
4) Workflow permissions and token hardening details
Most preventable CI/CD incidents trace back to overly broad permissions.
Practical checks
- Require explicit
permissionsin every workflow - Scope token rights per job, not globally where possible
- Remove unnecessary write scopes for build/test-only jobs
- Separate deploy jobs from test jobs with stricter approval paths
- Review reusable workflows for inherited permission expansion
Permission design pattern
| Job Type | Typical Needed Access | Hardening Notes |
|---|---|---|
| Lint/Test | Read repository contents | No write scopes required |
| Build Artifact | Read + artifact publish scope | Avoid repo/admin mutation permissions |
| Release Tagging | Controlled write for release process | Restrict to protected branch and approved context |
| Deployment | Environment-scoped credentials/permissions | Require approval gate and audited actor context |
5) Third-party actions and supply-chain trust
External actions accelerate delivery, but each one extends trust to external code.
Governance model
- Maintain approved action catalog
- Pin action versions to immutable references
- Require review before adding new external actions
- Track action owners and risk classification
- Periodically revalidate action necessity
Review checklist for external actions
- Is the source organization trusted and maintained?
- Is the action pinned to immutable version?
- Does it request privileged token scopes?
- Can the same task be achieved with native steps/internal action?
- Is there a fallback plan if action is deprecated or compromised?
6) Branch protection and deployment gating
Pipeline hardening fails if repository governance is weak.
Minimum branch and release controls
- Required reviews on protected branches
- Required status checks before merge
- Restricted bypass/override permissions
- Signed commit or provenance policy where appropriate
- Deployment jobs tied to protected environments
Deployment gate structure
| Stage | Required Controls |
|---|---|
| Development | Automated checks + basic policy validation |
| Staging | Additional security checks + owner review |
| Production | Manual approval + high-confidence status checks + audit logging |
This preserves release speed while reducing high-impact mistakes.
7) Secrets handling without leakage
Secrets in CI/CD should be treated like temporary, scoped assets.
Practical secrets controls
- Use environment-scoped secrets instead of global where possible
- Minimize which jobs can access each secret
- Rotate secrets on schedule and after incident suspicion
- Avoid passing secrets through unnecessary intermediate steps
- Monitor logs for accidental exposure patterns
Secret hygiene anti-patterns
| Bad Pattern | Better Practice |
|---|---|
| Reusing one broad secret for all environments | Separate secrets per environment with least scope |
| Logging command output without masking review | Use structured logging and masking validation |
| Long-lived cloud credentials in secrets | Prefer short-lived OIDC-based federated access patterns |
| Granting secrets to all workflow paths | Restrict to deployment paths with approvals |
8) Pull request workflow safety
PR workflows often become risk hotspots, especially in open or multi-contributor repos.
PR safety controls
- Restrict privileged steps from untrusted PR contexts
- Separate validation workflows from deployment-capable workflows
- Enforce conditions before sensitive jobs run
- Keep secrets inaccessible in lower-trust execution paths
Safe PR design principle
Treat contributor-submitted workflow context as lower trust until reviewed and merged.
9) Artifact and runner security
Artifacts and runners are frequently under-governed in smaller teams.
Artifact controls
- Define retention periods by sensitivity
- Limit artifact visibility and download permissions
- Validate integrity signals before deployment consumption
- Remove stale artifacts tied to old releases
Self-hosted runner controls
- Isolate runners from broad internal network access
- Use ephemeral runner patterns when practical
- Apply patching and baseline hardening controls to runner hosts
- Restrict who can target sensitive runner groups
- Ensure cleanup between jobs to avoid residue risks
Runner risk review table
| Runner Risk | Detection Signal | Mitigation |
|---|---|---|
| Persistent contamination between jobs | Unexpected files/processes after job completion | Ephemeral execution model + cleanup hooks |
| Excessive network reach | Jobs contacting unrelated internal services | Network segmentation and egress restrictions |
| Unauthorized workflow targeting | Sensitive runners used by low-trust workflows | Label restrictions and repo-level access policy |
| Patch lag | Known vulnerable packages on runner images | Image lifecycle and update cadence |
10) Build a secure workflow review process
Security should be part of normal PR/release operations, not a separate late-stage gate.
Review process design
- Define CI/CD control baseline and ownership
- Add checklist-based workflow reviews to PR templates
- Automate policy checks for risky patterns (broad permissions, floating refs)
- Require security review only for high-risk workflow changes
- Track exceptions with expiry and explicit owner
- Re-review critical workflows on regular schedule
Workflow change review matrix
| Change Type | Required Reviewer |
|---|---|
| Minor test step update | Repository maintainer |
| New third-party action | Security + maintainer |
| Permission expansion | Security + platform owner |
| Production deployment logic change | Security + release owner + team lead |
| Runner target change | Platform/security owner |
This keeps reviews proportional to risk and avoids unnecessary delivery friction.
11) Security–developer collaboration model
Hardening works when developers and security share outcomes, not when security only blocks changes.
Collaboration practices that scale
- Publish a “secure workflow starter” template
- Offer approved action catalog for common CI/CD tasks
- Use advisory checks first, then enforce high-risk controls gradually
- Share monthly pipeline risk dashboard with teams
- Run short incident retros focused on control improvements
Communication pattern
- Security provides control intent and risk context
- Developers provide workflow feasibility and release impact insight
- Platform team provides automation and policy enforcement path
12) Common mistakes in GitHub Actions hardening
- Broad default token permissions across all jobs
- Unpinned third-party actions in production workflows
- Secrets exposed through logs or unsafe step composition
- Untrusted PR paths reaching privileged execution contexts
- Deployments without environment approvals
- Self-hosted runners with excessive persistent trust
- No ownership for workflow security reviews
Fast anti-drift guardrails
- Block merge on high-risk workflow anti-patterns
- Require explicit permission blocks in new workflows
- Enforce action pinning policy in protected repositories
- Run quarterly workflow governance audit
13) 30-day GitHub Actions hardening roadmap
Week 1: Visibility and baseline inventory
- Inventory all workflows, tokens, external actions, runners, environments
- Classify workflows by risk level (test/build/deploy/admin)
- Identify top critical gaps (broad permissions, floating refs, unsafe triggers)
Output: CI/CD risk register v1
Week 2: High-risk control fixes
- Add explicit permissions to top critical workflows
- Pin high-risk third-party actions
- Tighten environment protections on production paths
Output: critical hardening change set
Week 3: Secrets and runner governance
- Scope secrets by environment and job necessity
- Review self-hosted runner segmentation and access controls
- Implement retention and visibility controls for artifacts
Output: secrets/runner governance update report
Week 4: Policy automation and operating cadence
- Add policy checks for risky workflow patterns
- Define recurring review schedule and ownership
- Publish secure workflow template and team guidance
Output: 30-day hardening completion report + next-quarter roadmap
14) Metrics to prove CI/CD hardening progress
| Metric | Why It Matters | Target Direction |
|---|---|---|
| % workflows with explicit permissions | Indicates least-privilege maturity | Up |
| % external actions pinned immutably | Supply-chain control strength | Up |
| Count of workflows with broad write token scope | Overprivilege indicator | Down |
| Secret exposure incidents in logs | Secret hygiene outcome signal | Down |
| % production deploy workflows with approval gates | Release governance coverage | Up |
| Mean time to review high-risk workflow changes | Operational efficiency indicator | Down |
A secure GitHub Actions program is an engineering system, not a one-time checklist: explicit permissions, trusted dependencies, scoped secrets, controlled runners, and a review process that keeps pace with shipping velocity.
CI/CD security operations worksheet
| Workstream | Owner | First Action | Validation Signal |
|---|---|---|---|
| Workflow permission hygiene | Platform security | Require explicit permission blocks in all workflows | Reduced overprivileged token usage |
| Third-party action governance | DevSecOps lead | Maintain approved action catalog with pinning policy | Fewer risky/unpinned action references |
| Runner hardening | Infrastructure owner | Segment and restrict runner groups by trust level | Lower runner misuse and lateral-risk exposure |
| Secrets management | Security + dev leads | Scope secrets by environment and job necessity | Reduced secret exposure in logs/incidents |
Weekly checklist
- Review new workflow changes for permission expansion
- Audit unpinned third-party actions in protected repos
- Validate environment approval flows for production jobs
- Track unresolved CI/CD security findings by owner
Workflow governance handoff pack
| Artifact | Minimum Content | Consumer |
|---|---|---|
| Workflow risk register | Workflow ID, risk category, owner, due date | Platform + security leadership |
| Policy exceptions | Justification, expiry, compensating controls | Governance/risk owners |
| Runner posture report | Access model, patch status, isolation controls | Infra + security teams |
| Monthly scorecard | Permission hygiene, pinning, secrets incidents | Engineering leadership |
Quality checks
- Are high-risk workflow changes reviewed before merge?
- Are policy exceptions time-bound and monitored?
- Are production deployment controls enforced consistently?
90-day CI/CD hardening cadence
Days 1–30
- Baseline all workflows, runners, and third-party actions
- Eliminate highest-risk permission and pinning gaps
- Establish monthly governance scorecard
Days 31–60
- Harden runner isolation and access boundaries
- Improve secret lifecycle controls and leak monitoring
- Add automated policy checks to pull request pipelines
Days 61–90
- Audit control drift and unresolved exceptions
- Tune enforcement thresholds to reduce developer friction
- Publish next-quarter CI/CD risk reduction roadmap
| KPI | Why It Matters |
|---|---|
| Workflows with explicit least-privilege permissions | Core access control maturity signal |
| Pinned third-party action coverage | Supply-chain governance indicator |
| Secrets exposure incidents | Operational control effectiveness metric |
| High-risk workflow review completion | Governance discipline measure |
CI/CD security improves most when engineering velocity and control maturity are managed together rather than as competing priorities.
Pipeline controls you can enforce (and how to keep them enforceable)
Hardening is not “one checklist.” It’s a set of enforceable guardrails that remain effective as repositories and teams evolve.
Mandatory controls (baseline)
| Control | Enforcement idea |
|---|---|
| Protected branches | Require PRs + reviews for default branch |
| Least-privilege tokens | Use fine-grained permissions per workflow |
| Trusted actions | Pin versions and restrict untrusted third-party actions |
| Secret handling | No plaintext secrets; rotate and audit |
| Build provenance | Generate attestations for critical artifacts |
Workflow review checklist (per repo)
- Does the workflow run on PRs from forks? If yes, are risky steps isolated?
- Are permissions explicitly declared at job/workflow scope?
- Are third-party actions pinned to immutable refs?
- Are artifacts signed or checksummed for release pipelines?
- Is there an owner who reviews CI changes (CODEOWNERS)?
Change management for CI
- Treat
.github/workflows/*as sensitive code: required review by a small group. - Maintain a “known-good” template for common workflows.
- Periodically review high-risk repos (release repos, infra repos, admin tooling).
Metrics that matter
| Metric | Why |
|---|---|
| Workflows with explicit permissions | Reduces accidental privilege |
| Unpinned third-party actions | Tracks supply-chain risk |
| Time-to-rotate secrets after incident | Tests operational readiness |
This makes GitHub Actions security professional: enforceable guardrails, controlled change, and measurable coverage.