A GCP environment becomes hard to secure when growth happens before guardrails. Teams add projects, service accounts, firewall rules, and storage buckets quickly, then try to retrofit governance later. That usually leads to privilege sprawl, weak visibility, and preventable exposure.
A baseline fixes this by defining the minimum controls that every project must meet before scaling.
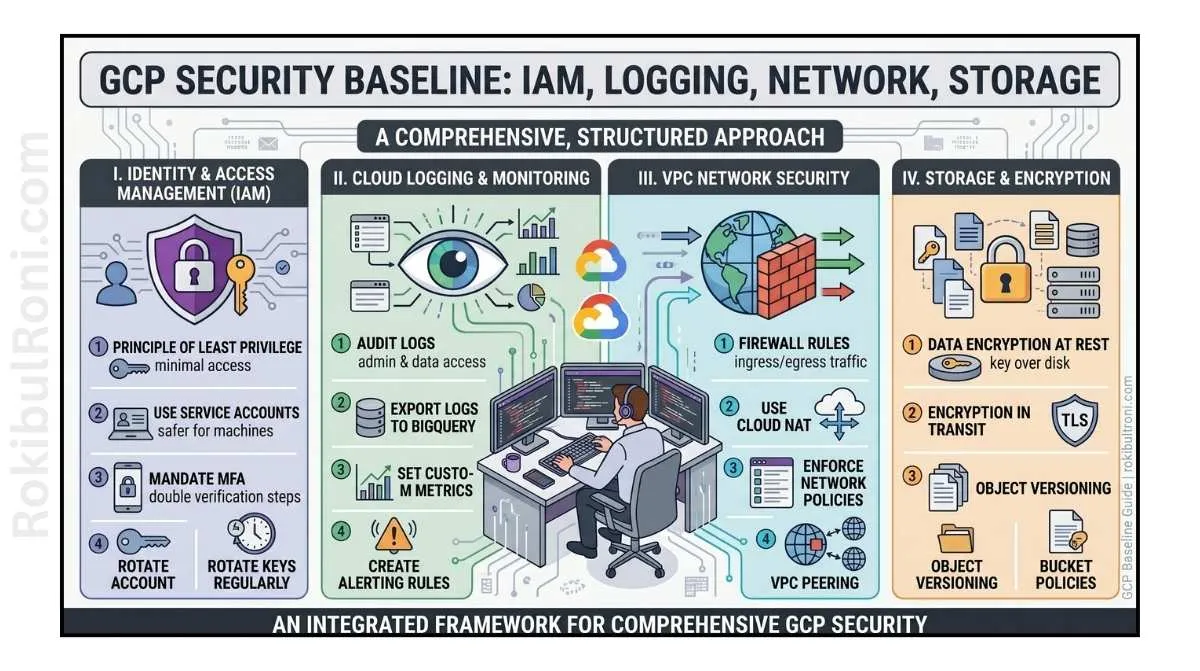
GCP security baseline
Use this guide as a defensive implementation framework for internal cloud hardening programs.
1) Why a GCP baseline should exist before cloud scale
- Prevents project sprawl and unmanaged ownership
- Reduces risk from broad IAM grants and unmanaged keys
- Ensures audit logs are available before incidents happen
- Aligns network exposure with business intent
- Creates consistent control expectations for engineering teams
A baseline is not a final-state architecture. It is the minimum safe operating standard.
2) Baseline domains you must standardize
Build baseline controls across these domains first:
- Organization and project hierarchy
- IAM roles, groups, and service-account governance
- MFA and identity assurance for privileged users
- Cloud Audit Logs and retention strategy
- VPC firewall and network segmentation
- Cloud Storage exposure and access control
- Public exposure detection and remediation
- Secret handling and key-management hygiene
- Compute and container hardening essentials
- Billing alerts and cost anomaly security signals
Baseline dependency logic
Identity + logging + network controls should be established before broad workload rollout. If that order is reversed, risk grows faster than governance.
3) GCP baseline checklist table (required)
| Baseline Control Area | Minimum Standard | Validation Method | Owner |
|---|---|---|---|
| Organization Structure | Projects grouped by environment/business function with clear ownership | Org/project inventory review | Cloud platform owner |
| IAM Role Design | Least-privilege roles; no unnecessary Owner role assignments | IAM bindings audit | IAM/security team |
| Service Accounts | Dedicated service accounts per workload with scoped permissions | Service account inventory + policy review | Platform engineering |
| MFA Enforcement | MFA required for privileged access paths | Identity policy verification | Identity admin |
| Cloud Audit Logs | Admin activity and data-access logs enabled where required | Logging policy and sink checks | Security operations |
| VPC Firewall Rules | Ingress/egress aligned to approved services only | Firewall rule audit + change review | Network/cloud ops |
| Cloud Storage Security | Buckets private by default with explicit exceptions | Bucket ACL/IAM policy scan | Data/platform owner |
| Public Exposure Control | External endpoints inventoried and reviewed | Exposure report + owner confirmation | Cloud security |
| Secrets Management | No secrets in code/env where avoidable; managed secret storage used | CI scan + config review | DevSecOps |
| Compute Hardening | Baseline images, patch process, and metadata protections | Image/policy compliance checks | Compute owner |
| Container Security | Workload identity, least privilege, and image scanning controls | Cluster and CI policy checks | Kubernetes/platform team |
| Billing & Alerting | Budget alerts and anomaly monitoring enabled | Billing config review | FinOps + security |
This table should be used as a recurring governance artifact, not only onboarding documentation.
4) Practical risk prioritization for GCP hardening
Not all gaps are equal. Prioritize fixes by exposure + privilege + impact.
Highest-priority risk categories
- Public exposure with weak access controls
- Privileged identities with broad or unmanaged access
- Missing or incomplete audit logging
- Unmanaged service-account keys and stale credentials
- Overly permissive firewall rules
Priority matrix
| Risk Pattern | Likelihood | Business Impact | Priority |
|---|---|---|---|
| Public bucket with sensitive data potential | High | High | Critical |
| Excessive Owner role usage across projects | Medium-High | High | High |
| Missing audit logs for privileged actions | Medium | High | High |
| Stale service-account keys in automation | Medium | Medium-High | High |
| Broad firewall ingress on non-public services | Medium | High | High |
| Project naming/ownership inconsistency | High | Medium | Medium |
If two or more high-priority risks exist simultaneously in production, escalate baseline remediation as an urgent program, not a background task.
5) Tooling workflow for baseline assessments
Use tooling for visibility and repeatability, then validate manually before major changes.
Recommended tools and their practical role
| Tool / Platform | Practical Use in Baseline Work |
|---|---|
gcloud CLI | Controlled inventory, policy inspection, and validation commands |
| Security Command Center (concept) | Centralized misconfiguration and exposure signal aggregation |
| Cloud Asset Inventory (concept) | Asset ownership, IAM, and configuration relationship mapping |
| Cloud Logging | Audit event review and control verification |
| Cloud Monitoring | Operational signal and alerting alignment |
| SIEM export pipeline | Cross-domain correlation and long-term incident analysis |
Assessment sequence
- Pull asset and IAM inventory.
- Compare against baseline checklist controls.
- Score gaps by risk priority.
- Validate findings with service owners.
- Plan phased remediation with rollback readiness.
6) IAM baseline specifics for GCP
IAM drift is usually the largest long-term cloud risk.
IAM hardening controls
- Minimize use of primitive roles (
Owner, broadEditorpatterns) - Use group-based access over direct user bindings where possible
- Scope role assignments at the lowest practical resource level
- Separate human admin identities from workload identities
- Review service-account usage and rotate/remove stale keys
- Enforce approval process for privileged role grants
IAM review table
| IAM Check | What to Look For | Action |
|---|---|---|
| Primitive role overuse | Excess Owner/broad role bindings | Replace with scoped predefined/custom roles |
| Direct user privilege grants | Individual high-privilege bindings | Migrate to managed groups with approval workflow |
| Service account sprawl | Unclear ownership and role purpose | Tag ownership and reduce role scope |
| Key hygiene issues | Old or unused service-account keys | Rotate/revoke and prefer keyless patterns |
7) Logging baseline and retention discipline
Without reliable logs, incident response becomes guesswork.
Logging baseline controls
- Enable required Cloud Audit Logs at org/folder/project scope
- Ensure log sinks route critical events to durable storage/SIEM
- Define retention periods aligned with policy/regulatory needs
- Protect log integrity with access controls and separation of duties
- Monitor for logging pipeline failures and dropped events
Logging health signals
| Signal | Interpretation | Follow-up |
|---|---|---|
| Sudden drop in auth/admin events | Ingestion or configuration drift | Validate sinks and logging policies immediately |
| Missing events for privileged operations | Coverage gap in audit configuration | Correct log type enablement and re-verify |
| High delay between event and availability | Pipeline latency issue | Tune routing and processing path |
8) Network and storage baseline controls
Cloud attack surface is often exposure by misconfiguration, not advanced technique.
Network baseline essentials
- Deny-by-default ingress where practical
- Restrict management interfaces to approved paths
- Segment workloads by environment and trust level
- Review egress controls for sensitive workloads
- Document every exception with owner and expiry date
Storage baseline essentials
- Private-by-default bucket policy
- Explicitly controlled public access exceptions
- Principle of least privilege for bucket/object access
- Monitoring for policy/ACL drift
- Classification-aware access and retention controls
Exposure control table
| Area | High-Risk Pattern | Baseline Expectation |
|---|---|---|
| VPC Firewall | Broad internet ingress to internal services | Explicit allow rules only for required sources/services |
| Admin Access Paths | Direct broad admin access from public internet | Controlled access with strict identity and network controls |
| Cloud Storage | Public bucket by default behavior | Public access disabled unless approved exception |
| Inter-project Connectivity | Untracked trust paths across projects | Documented and reviewed connectivity policies |
9) How to document and manage exceptions
Some deviations are necessary. Untracked exceptions become hidden risk.
Exception record minimum fields
- Control being bypassed
- Business justification
- Risk acceptance owner
- Compensating controls in place
- Expiration date and review schedule
- Validation evidence
Exception governance table
| Exception Attribute | Required Value |
|---|---|
| Approval | Named accountable manager + security reviewer |
| Duration | Time-bounded with review date |
| Compensating Control | Documented technical/operational mitigation |
| Visibility | Included in monthly governance reporting |
| Closure Criteria | Defined condition to remove exception |
No permanent exceptions without periodic executive-level review.
10) Common GCP baseline mistakes
- Project sprawl without ownership conventions
- Overuse of Owner-level access for convenience
- Public bucket exposure from weak default controls
- Missing log retention and pipeline validation
- Unused service-account keys left active
- Firewall rules broadened during incident/change windows and never reverted
- Baseline documented once but not operationalized
Anti-drift guardrails
- Monthly baseline conformance review
- Change-control integration for IAM/network/storage changes
- Automated checks in CI/CD where possible
- Quarterly exception review and cleanup
11) 30-day GCP hardening roadmap
Week 1: Establish visibility and ownership
- Inventory projects, identities, service accounts, and buckets
- Tag owners and classify critical workloads
- Identify top public exposure and privilege risks
Output: baseline gap register v1
Week 2: Address critical identity and exposure gaps
- Reduce high-risk IAM grants
- Lock down public storage exposures
- Tighten highest-risk firewall rules
Output: critical-risk remediation change set
Week 3: Logging, monitoring, and detection alignment
- Validate audit log coverage and sink reliability
- Integrate high-value signals into SIEM workflows
- Add alerts for privileged changes and exposure drift
Output: logging assurance and detection baseline report
Week 4: Governance hardening and sustainability
- Implement exception register and review cadence
- Finalize baseline policy documentation
- Present status, residual risk, and next-quarter priorities
Output: 30-day hardening completion report + roadmap
12) Metrics that show baseline maturity
| Metric | Why It Matters | Target Direction |
|---|---|---|
| % projects with defined owner tags | Governance foundation signal | Up |
| % privileged identities with MFA | Identity assurance maturity | Up |
| Count of public-exposure exceptions | Exposure risk indicator | Down |
| % service accounts with recent key rotation or keyless pattern | Credential hygiene quality | Up |
| Audit-log coverage across critical projects | Incident readiness quality | Up |
| Mean time to remediate critical baseline gaps | Program execution speed | Down |
A strong GCP baseline is not a checklist done once. It is an operating rhythm: consistent control definitions, clear owners, evidence-backed validation, and recurring reviews that keep cloud growth inside safe boundaries.
Baseline operations worksheet for GCP teams
| Workstream | Owner | First Action | Validation Signal |
|---|---|---|---|
| Project governance | Cloud platform lead | Enforce naming/owner standards for all projects | Fewer orphaned or ambiguous projects |
| IAM hygiene | Identity admin | Audit primitive role usage and stale service accounts | Reduced broad-access assignments |
| Logging assurance | Security operations | Validate audit log coverage and sink integrity | Reliable event visibility for critical actions |
| Exposure control | Cloud security engineer | Review public endpoints and bucket exposures weekly | Faster closure of accidental exposure findings |
Governance checklist
- Confirm owner mapping for new projects and critical resources
- Validate exception register updates and expiry dates
- Review firewall and storage changes for drift
- Track unresolved high-priority baseline gaps
Control validation and handoff pack
| Artifact | Minimum Content | Consumer |
|---|---|---|
| Baseline gap register | Control gap, risk level, owner, due date | Security + platform leads |
| Validation evidence | Commands/screenshots/log references per control | Audit and governance teams |
| Exception record | Justification, compensating controls, expiry | Risk owners |
| Quarterly status brief | Progress trends and unresolved risk clusters | Leadership stakeholders |
Quality checks
- Are critical baseline gaps assigned with realistic deadlines?
- Can each claimed control be validated with evidence?
- Are exceptions reducing over time or accumulating without closure?
90-day GCP baseline execution cadence
Days 1–30
- Reconcile project inventory and owner mapping
- Prioritize and close top critical exposure and IAM gaps
- Validate required logging controls across high-value projects
Days 31–60
- Harden firewall and storage controls in remaining high-risk projects
- Improve service-account governance and key hygiene
- Build recurring compliance checks into change workflows
Days 61–90
- Run quarterly baseline conformance review
- Measure risk reduction and unresolved exception trends
- Publish roadmap for next-cycle hardening improvements
| KPI | Why It Matters |
|---|---|
| Projects with complete owner metadata | Governance completeness indicator |
| Critical baseline gaps closed | Core hardening progress metric |
| Exception count with valid expiry | Exception control maturity |
| Audit-log coverage on critical projects | Incident readiness quality |
Baseline maturity grows when teams combine technical controls, governance ownership, and recurring validation into a stable operating model.
Baseline verification and drift management (GCP)
A baseline is only meaningful if you continuously verify it. The fastest way to lose security posture in GCP is to treat baseline work as a one-time setup.
Drift signals to monitor
| Area | Drift signal | Why it matters |
|---|---|---|
| IAM | New high-privilege bindings or broad roles | Expands blast radius quickly |
| Logging | Disabled sinks/audit logs, reduced retention | Removes investigation capability |
| Network | New public IPs / firewall rule expansions | Increases exposure |
| Storage | Buckets becoming public or policy weakened | Data leakage risk |
Baseline evidence pack (for audits and reviews)
- IAM review summary (principals, privileged roles, exceptions).
- Logging configuration snapshot (audit log settings, sinks, retention).
- Network exposure summary (public services, firewall highlights).
- Storage posture summary (public access controls, encryption defaults).
Change management standards
- Any change that introduces public exposure or elevated privileges requires explicit owner approval.
- Exceptions are time-boxed with an expiry and follow-up ticket.
- Review baseline controls on a fixed cadence (monthly for critical projects, quarterly otherwise).
KPIs that reflect real baseline health
| KPI | Target direction |
|---|---|
| Privileged principals without justification | Down |
| Logging coverage for critical projects | Up |
| Publicly exposed services without documented owner | Down to zero |
| Baseline exceptions past expiry | Down to zero |
This is how you keep the baseline professional: verifiable controls, measurable posture, and strict handling of drift and exceptions.