Cloud security is often marketed as a futuristic job where a dashboard finds the threat, an AI model explains it, and a button fixes the incident. Real cloud security is more practical and more interesting than that. It is architecture review, identity design, logging, automation, incident response, and the discipline to keep fast-moving infrastructure from becoming an attacker playground.
The old network perimeter is not enough anymore. In a cloud environment, a developer can create a database, expose a storage bucket, attach a powerful role to a virtual machine, or open a route to the internet in minutes. That speed is the reason cloud exists, but it is also the reason cloud security engineers must think like builders, auditors, and defenders at the same time.
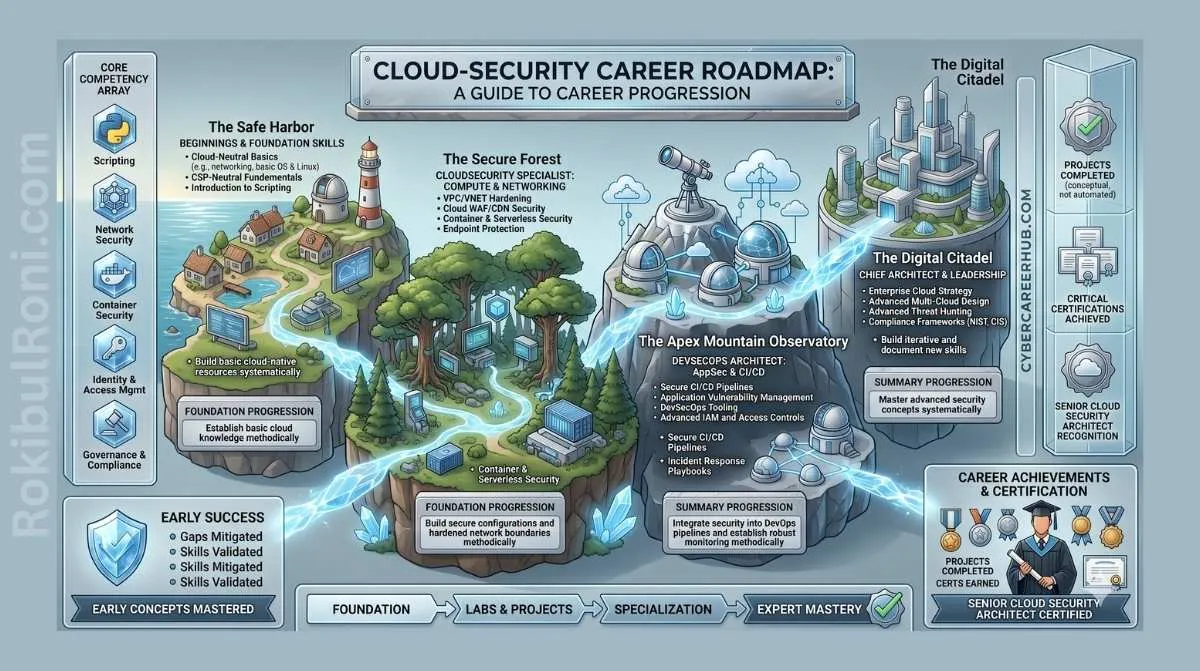
This roadmap turns the raw career idea into a practical plan. If you want to enter cloud security, your goal is not to memorize every service name. Your goal is to understand how cloud systems are built, how they fail, how attackers abuse misconfigurations, and how to automate guardrails before mistakes reach production.
What Cloud Security Really Means
Cloud security is not one job. It is a cluster of related work that sits between infrastructure, software engineering, security operations, and governance.
At the entry level, you might review security group rules, investigate alerts, rotate stale access keys, document risky configurations, and run posture scans. At the engineer level, you might design landing zones, write Terraform modules, build CI/CD controls, automate remediation, tune GuardDuty or Microsoft Defender for Cloud findings, and help incident responders reconstruct attacker activity from logs.
The best mindset is simple: cloud security is defensive engineering. You are not only telling people what is wrong. You are building repeatable systems that make the secure path easier than the insecure path.
| Area | What It Means | Why It Matters |
|---|---|---|
| Architecture | VPCs, subnets, routing, accounts, projects, and landing zones | Most cloud breaches begin with weak design or unsafe defaults |
| Identity | Users, roles, service accounts, policies, permissions, and trust | Identity is the real cloud perimeter |
| Data protection | Encryption, storage access, backups, secrets, and key management | Cloud platforms make data easy to copy, expose, and share |
| Logging | CloudTrail, activity logs, audit logs, DNS logs, flow logs, and SIEM pipelines | You cannot investigate what you did not collect |
| Automation | Terraform, policy as code, serverless response, and CI/CD checks | Manual cloud security does not scale |
| Operations | Alert triage, incident response, evidence capture, and remediation | Security must survive real incidents, not just audits |
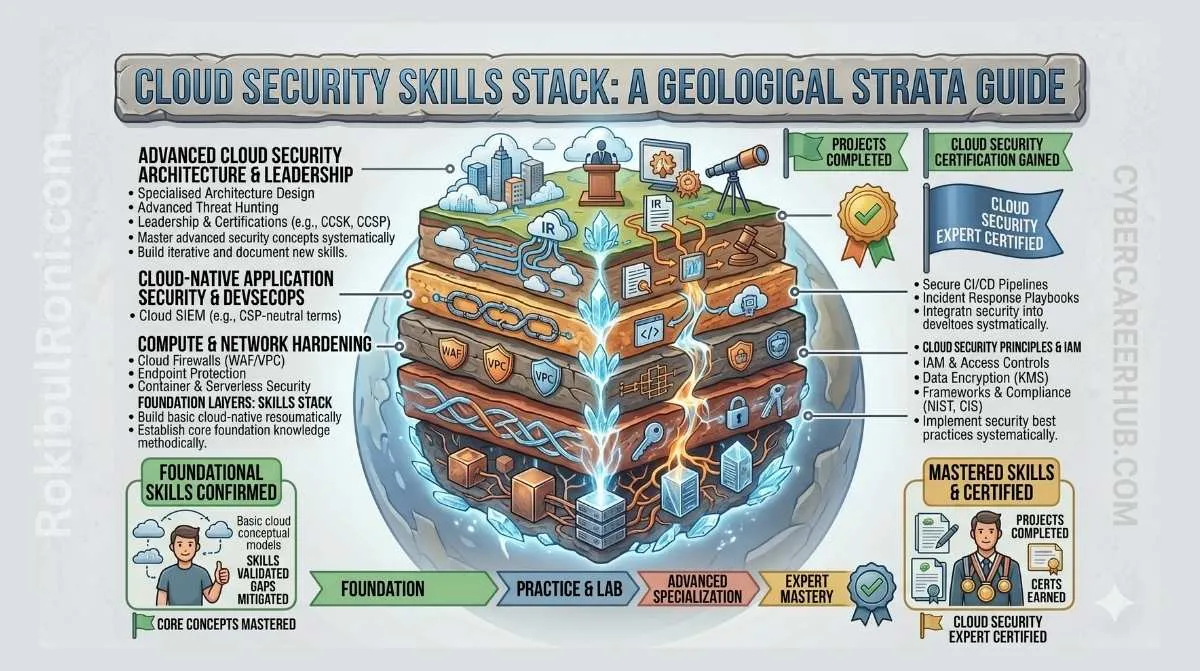
The Foundational Skills That Matter Most
You cannot secure what you do not understand. Beginners often jump into advanced cloud threat hunting before they can explain how a subnet route table works. That creates shallow knowledge. Build the base first.
1. Networking in the Cloud
Cloud networking hides the cables, but the logic remains. You need to understand:
- How VPCs and virtual networks isolate resources
- How public and private subnets differ
- How route tables decide where traffic goes
- How security groups differ from network ACLs
- How load balancers, NAT gateways, VPNs, and private endpoints change exposure
- How DNS can route users to the wrong place or reveal sensitive infrastructure
If a database is deployed in a public subnet with inbound access from 0.0.0.0/0, you should immediately understand why it is dangerous, how to prove the risk, and how to fix it without breaking the application.
2. Identity and Access Management
In the cloud, identity is the new perimeter. A small server compromise becomes a major breach if that server has an overpowered role attached to it.
Learn how to read IAM policies, trust policies, permission boundaries, service principals, managed identities, and resource-based policies. The principle of least privilege is not a slogan. It means giving a human, service, function, or workload exactly the actions it needs on exactly the resources it needs under the right conditions.
AWS recommends applying least privilege and using tools such as IAM Access Analyzer to refine permissions based on access activity. That is the type of practical advice you should turn into labs, scripts, and portfolio evidence.
3. Linux, APIs, and Scripting
Most cloud workloads run on Linux, and most cloud platforms are controlled through APIs. You need enough Linux to inspect systems, read logs, manage permissions, and troubleshoot services. You also need enough scripting to automate checks.
Python is the safest first language for cloud security automation. Use it to call APIs, parse JSON, query assets, detect insecure settings, and trigger remediation. Bash is still useful for quick Linux tasks, local tooling, and glue scripts.
4. Infrastructure as Code
Modern companies do not build cloud environments by clicking around forever. They define infrastructure in code. Terraform is a common industry standard because it lets teams define, version, review, and reuse infrastructure configuration.
For a cloud security career, this matters because the best time to catch a bad security group, unencrypted bucket, public database, or hardcoded secret is before deployment. Tools such as Checkov can scan infrastructure as code for misconfigurations and policy violations. This turns security from a late audit into an early engineering control.
The Tools You Should Learn
Do not try to learn every cloud security product at once. Start with the tools that teach transferable concepts. If you know why a tool exists, you can learn a competing tool later.
| Skill Area | Learn First | Why It Helps |
|---|---|---|
| Cloud provider | AWS or Azure first, then add GCP | Most jobs want depth in at least one major platform |
| Infrastructure as code | Terraform | Helps you review, deploy, and secure repeatable infrastructure |
| IaC scanning | Checkov or tfsec | Finds misconfigurations before deployment |
| Posture scanning | Prowler, ScoutSuite, CloudSploit, or Defender CSPM | Shows real account risks against security benchmarks |
| Logging | AWS CloudTrail, Azure Activity Log, GCP Audit Logs | Gives evidence for investigation and compliance |
| Detection | Amazon GuardDuty, Microsoft Defender for Cloud, Security Command Center | Teaches cloud-native threat detection patterns |
| Querying | Athena SQL, KQL, BigQuery, Splunk SPL | Lets you search large log sets during investigations |
| Automation | Python SDKs, Lambda, EventBridge, Azure Functions, Logic Apps | Lets you turn response playbooks into repeatable controls |
| Secrets | AWS Secrets Manager, Azure Key Vault, Google Secret Manager | Prevents hardcoded secrets and weak key handling |
Native logging deserves special attention. AWS CloudTrail records API activity and includes details such as who made a request, when it happened, source IP, request parameters, and response data. When someone disables logging, changes a role, creates access keys, or snapshots a database, those events are the investigation trail.
Threat detection tools are also important, but do not treat them as magic. Amazon GuardDuty, for example, monitors AWS accounts and workloads for malicious activity, unauthorized behavior, unusual API calls, malware indicators, and suspicious network activity. Your value as an engineer is knowing what the alert means, what logs support it, what blast radius exists, and what remediation is safe.
A Practical Roadmap From Beginner to Cloud Security Engineer
This roadmap is intentionally sequential. You can move faster or slower, but do not skip the foundations.
Phase 1: IT, Linux, and Networking
Build basic operational confidence first.
- Use Linux daily for file navigation, permissions, services, logs, SSH, and shell scripting
- Learn TCP/IP, DNS, HTTP, TLS, routing, ports, and subnets
- Understand how a web request reaches a server
- Practice reading firewall logs and web server logs
- Build a small local lab with a Linux VM and a web service
Your milestone: explain how a user reaches a web application and where security controls can inspect, block, log, or encrypt that traffic.
Phase 2: Cloud Builder Basics
Pick one provider first. AWS is a safe starting point because of market demand and learning resources. Azure is equally valuable in enterprise environments. GCP is strong for data, Kubernetes, and platform engineering teams.
Build before securing:
- Create a free tier account or sandbox account
- Host a static website
- Deploy a virtual machine
- Connect a web tier to a database
- Create a private subnet and a public subnet
- Enable basic logging
- Break the setup, then troubleshoot it
Your milestone: deploy a small cloud application and draw its architecture from memory.
Phase 3: Security Fundamentals and IAM
Now revisit what you built and secure it.
- Remove public access where it is not required
- Encrypt storage and databases
- Enable audit logs
- Create least privilege roles
- Write a custom IAM policy
- Test allowed and denied actions
- Use posture scanning to identify mistakes
Your milestone: explain every permission your workload has and why each one is required.
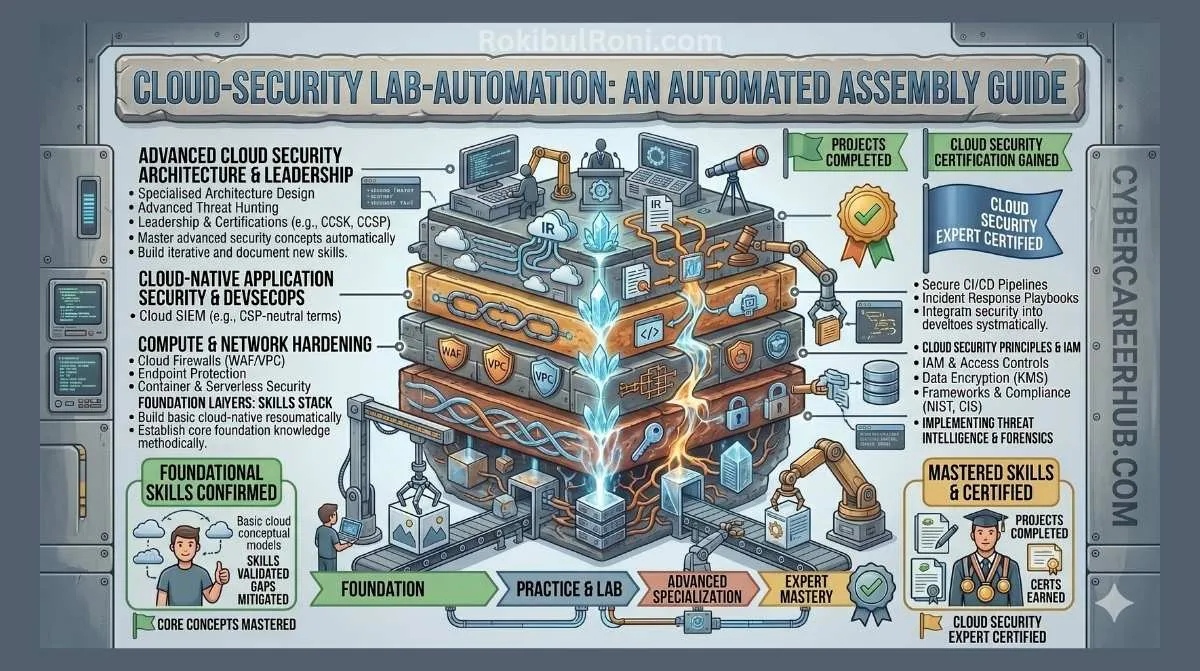
Phase 4: Terraform and Policy as Code
Stop using the console as your primary build method. Rebuild the same environment using Terraform.
- Write Terraform for networking, compute, storage, and IAM
- Store the code in Git
- Run
terraform fmt,terraform validate, and a security scanner - Add CI/CD checks with GitHub Actions
- Fail the pipeline when high-risk misconfigurations appear
Your milestone: a reviewer can clone your repo, read your code, and understand how your cloud environment is built and secured.
Phase 5: Detection and Automated Response
Security teams need people who can close the loop from alert to action.
- Enable cloud-native detection
- Send findings to an event bus or SIEM
- Write a Python function that reacts to a specific event
- Tag, isolate, or remediate a risky resource
- Notify a Slack channel, email inbox, or ticket queue
- Document what happens and what should not be automated
Your milestone: one real cloud security event triggers one safe, auditable response.
Three Portfolio Labs That Can Get You Interviews
Certifications help you pass filters. A portfolio helps you pass technical interviews. Build projects that mirror real work.
Lab 1: Automated Security Group Remediation
Create an AWS lab where a security group rule that opens SSH to the internet is detected and removed.
Your architecture:
- Terraform creates the VPC, security group, EventBridge rule, Lambda function, and notification target
- CloudTrail records the API call
- EventBridge matches the risky security group change
- Lambda checks the rule and removes open SSH access
- The function writes a clear log message and sends an alert
What to document:
- Architecture diagram
- Terraform structure
- Python remediation logic
- Before and after screenshots
- Safety notes, including when automated remediation can break production
Lab 2: IAM Credential Auditor
Write a Python script that checks IAM users and access keys.
Minimum version:
- List IAM users
- Identify access keys older than 90 days
- Export the username, key ID, and age to CSV
- Print a summary of risky accounts
Advanced version:
- Detect unused keys
- Flag users without MFA
- Add a dry-run mode
- Deactivate keys older than 120 days only when explicitly approved
This lab proves you understand both cloud identity risk and safe automation.
Lab 3: Secure Terraform Pipeline
Create a small Terraform repo with deliberate flaws, then block them in CI/CD.
Include examples such as:
- Public storage bucket
- Unencrypted database
- Overly permissive security group
- Hardcoded test secret
- IAM policy with wildcard actions
Then configure GitHub Actions to run Checkov or tfsec. The pipeline should fail when high-risk issues exist and pass after you fix them.
This lab is powerful because it shows DevSecOps thinking: prevent the problem before it becomes a production incident.
Certification Strategy Without Wasting Money
Certifications are useful when they match your stage. Do not collect random badges. Use them to structure learning and signal readiness.
| Stage | Useful Certifications | Best Use |
|---|---|---|
| Beginner | CompTIA Network+, CompTIA Security+, AWS Cloud Practitioner, Microsoft SC-900 | Build vocabulary and pass entry-level filters |
| Cloud foundation | AWS Solutions Architect Associate, Azure Administrator Associate, Google Associate Cloud Engineer | Prove you can build cloud systems |
| Cloud security | AWS Certified Security - Specialty, Azure Security Engineer Associate, Google Professional Cloud Security Engineer | Prove provider-specific security skill |
| Vendor-neutral cloud security | CSA CCSK, ISC2 CCSP | Show broader governance, architecture, and cloud security knowledge |
| Senior architecture | Microsoft SC-100, CISSP, SABSA, security architecture training | Support architecture, leadership, and governance roles |
As of April 2026, ISC2 notes that the CCSP exam outline will change on August 1, 2026. If CCSP is on your plan, check the official outline before buying training. Microsoft also updates certification exams regularly, including SC-100 in April 2026. Certification pages should be treated as living documents, not static blog advice.
The smartest path for most beginners is:
- Learn networking and Linux.
- Earn Security+ only if your job market values it.
- Get one cloud associate certification after you can actually build.
- Build two portfolio labs.
- Add a cloud security certification when you can explain real risks, not just exam terms.
Where the Jobs Are
Many beginners only look at big technology companies and cybersecurity vendors. Those are good targets, but they are not the only path.
Cloud adoption is aggressive in finance, healthcare, telecom, manufacturing, engineering, construction, logistics, education, government suppliers, and data center operations. These organizations often have complex hybrid environments, legacy systems, compliance pressure, and urgent cloud migration projects. That combination creates real demand for people who can secure cloud infrastructure without slowing delivery to a crawl.
In markets such as Malaysia and Singapore, cloud security roles can appear under many titles:
- Cloud Security Analyst
- Cloud Security Engineer
- DevSecOps Engineer
- Security Automation Engineer
- Cloud SOC Analyst
- IAM Engineer
- Security Architect
- Cloud Compliance Analyst
- Infrastructure Security Engineer
Do not reject a role just because the title is imperfect. Read the responsibilities. If the job includes IAM, cloud logging, Terraform, detection, CI/CD, vulnerability management, or incident response, it can build the right experience.
How to Answer Cloud Security Interview Scenarios
Interviewers want to know whether you can think through risk. For example:
A detection tool reports that an EC2 instance might be compromised. What do you do?
A weak answer is: “I would check the dashboard and block the attacker.”
A strong answer sounds more like this:
- Confirm the alert source, severity, affected account, region, instance ID, role, public IP, and timeline.
- Preserve evidence by capturing relevant logs and taking a snapshot according to the incident response process.
- Contain the instance by changing security groups, isolating network routes, or moving it into a quarantine workflow.
- Check CloudTrail for suspicious API calls from the instance role or related identities.
- Review GuardDuty findings, VPC flow logs, DNS logs, authentication logs, and recent deployment changes.
- Identify whether credentials, data, or other systems were accessed.
- Rotate exposed credentials and remove risky permissions.
- Rebuild from a clean image instead of trusting a compromised host.
- Document root cause, impact, remediation, and detection improvements.
That answer shows architecture thinking, logging awareness, containment discipline, and cloud-specific knowledge.
A 90 Day Study Plan
If you want a clear start, use this 90 day plan.
| Days | Focus | Output |
|---|---|---|
| 1-15 | Linux, networking, DNS, HTTP, TLS, and subnetting | Notes, command cheatsheet, small Linux web server |
| 16-30 | Cloud builder basics | Static site, VM, database, public and private subnet diagram |
| 31-45 | IAM and logging | Custom IAM policies, CloudTrail or activity log queries |
| 46-60 | Terraform | Rebuild your lab using infrastructure as code |
| 61-75 | Scanning and CI/CD | Checkov or tfsec pipeline that blocks risky Terraform |
| 76-90 | Automated response | Event-driven remediation lab with documentation |
By the end, you should have one polished GitHub repository, one architecture diagram, one recorded demo or screenshot set, and one clear write-up explaining tradeoffs. That is far stronger than saying you watched a course.
Official References Worth Bookmarking
- AWS IAM security best practices
- AWS CloudTrail documentation
- Amazon GuardDuty documentation
- Terraform introduction
- Checkov documentation
- Prowler documentation
- Microsoft Defender Cloud Security Posture Management
- ISC2 CCSP certification
- CSA CCSK v5 FAQ
- Google Professional Cloud Security Engineer
Final Advice
The cloud security path does not require genius. It requires patient technical depth. Build things, break things, read logs, fix permissions, automate the boring checks, and document the lessons.
The people who grow fastest are not the people who know the most service names. They are the people who can look at a cloud architecture and answer four questions:
- What can reach this system?
- What identity can this system use?
- What data can it access?
- What evidence will exist if it is abused?
If you can answer those questions with confidence and prove it through labs, you are already moving like a cloud security engineer.