Public applications are continuously scanned, probed, and abused, even when they are small. Attackers do not need to know your brand size; they only need a reachable endpoint with weak controls.
Cloudflare helps reduce exposure at the edge, but only when controls are configured as part of a broader defense strategy. Edge controls should reduce risk before traffic reaches origin, not replace origin hardening.
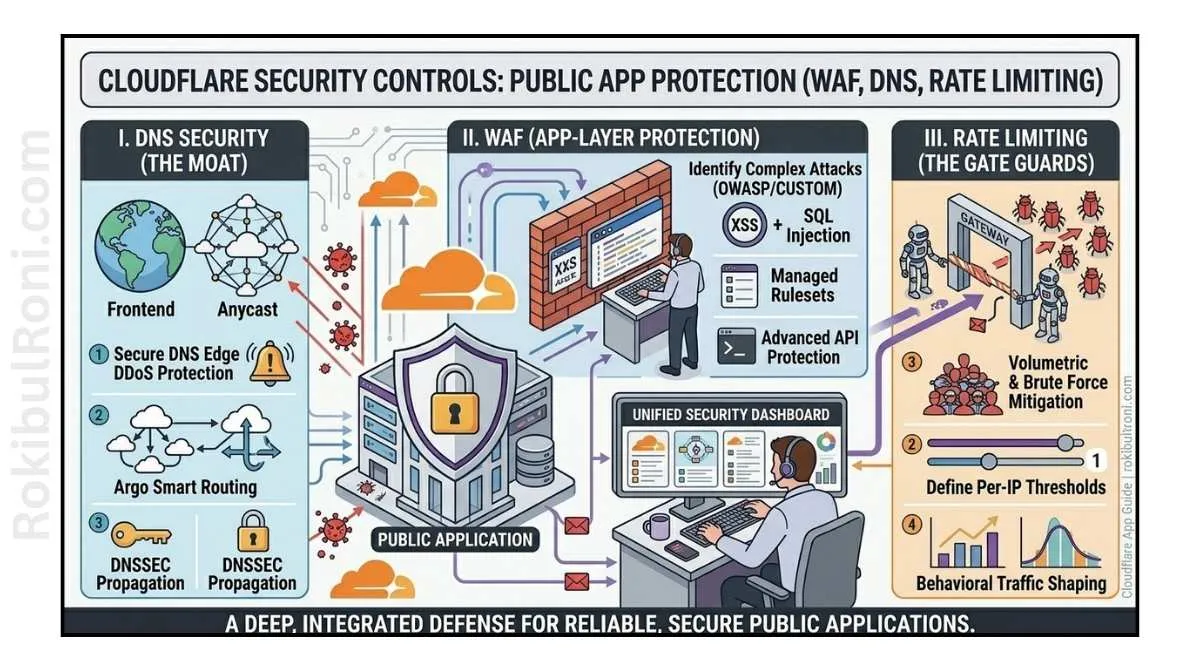
Cloudflare security controls for public apps
Use this as a practical baseline for SaaS teams, small businesses, and personal brand applications.
1) Why public apps need edge security controls
- Internet-facing apps receive constant automated probing
- Weak TLS/DNS configurations can expose sessions and infrastructure metadata
- Missing rate limits makes API and login abuse cheaper for attackers
- Unprotected admin paths are common compromise entry points
- Inadequate logging delays incident response and containment
Edge controls improve survivability, but only when paired with application and infrastructure hardening.
2) Core control categories to configure first
Start with controls that reduce the largest exposure risks quickly:
- DNS hygiene and record governance
- Proxying and origin IP protection
- TLS mode and certificate posture
- WAF managed rules and targeted custom rules
- Bot management concepts and abuse controls
- Rate limiting by endpoint sensitivity
- DDoS posture and traffic handling strategy
- Security headers and response hardening
- Rules/configuration hygiene (page/config rule discipline)
- Zero Trust Access concept for admin-facing surfaces
- Log export and monitoring integration
3) Cloudflare control table (required)
| Control | Threat Reduced | Recommended Use | Operational Note |
|---|---|---|---|
| DNS Hygiene | Domain takeover drift, stale records, misrouting | Keep records minimal, current, and ownership-tracked | Review stale/unused records monthly |
| Proxy Enablement | Direct origin exposure, bypass attempts | Proxy public application records by default where applicable | Validate origin is not reachable directly |
| TLS Configuration | Session interception and weak crypto posture | Enforce modern TLS settings and strict HTTPS behavior | Test compatibility before strict mode rollout |
| WAF Managed Rules | Known web attack classes and common probes | Start with managed baseline and monitor impact | Tune based on false positives and app behavior |
| Custom WAF Rules | App-specific abuse not covered by generic rules | Protect sensitive paths and high-risk methods/params | Keep rules documented with owner and review date |
| Bot Protection (concept) | Credential stuffing, scraping, automated abuse | Apply graduated controls on sensitive endpoints | Tune to avoid blocking valid automated clients |
| Rate Limiting | Brute-force, API burst abuse, resource exhaustion | Set endpoint-specific thresholds by function risk | Different limits for login, search, and API write paths |
| DDoS Protection | Traffic flood disruption at edge and app layers | Keep baseline protections active and monitored | Pair with origin scaling/failover planning |
| Security Headers | Browser-side exposure and weak client protections | Standardize header policy for public responses | Validate header changes against app functionality |
| Rules/Config Governance | Misconfiguration drift and policy collisions | Use clear rule ordering and change tracking | Audit rule sprawl regularly |
| Zero Trust Access (concept) | Unauthorized access to admin portals/tools | Require identity-based access for non-public admin surfaces | Keep break-glass process documented |
| Log Integration | Delayed detection and poor IR visibility | Export edge/security logs to SIEM or log platform | Normalize fields for triage workflows |
4) DNS and origin protection fundamentals
Many public-app incidents start with DNS and origin exposure mistakes.
DNS hygiene controls
- Keep authoritative records documented with owner/team context
- Remove stale records tied to retired infrastructure
- Validate CNAME/target lifecycle when services are decommissioned
- Monitor for unauthorized or unexpected record changes
Origin exposure controls
- Keep origin IPs private where possible
- Restrict direct origin access to trusted pathways only
- Use firewall/network controls so traffic must pass through edge protections
- Verify bypass resistance after major network or hosting changes
If origin remains reachable directly, edge protections can be bypassed.
5) TLS and transport security choices
TLS settings determine how safely traffic reaches your edge and origin.
Practical TLS baseline
- Redirect HTTP to HTTPS consistently
- Disable weak protocol/cipher patterns where feasible
- Use strict encryption posture between edge and origin
- Monitor certificate validity and renewal paths
TLS validation checklist
| Check | Why It Matters |
|---|---|
| HTTPS enforced globally | Prevents plaintext exposure |
| Secure edge-to-origin mode | Reduces downgrade and interception risk |
| Valid certificate lifecycle monitoring | Prevents service interruptions and trust failures |
| HSTS/transport behavior reviewed | Strengthens client-side transport expectations |
Roll out strict settings in staged fashion to prevent avoidable outages.
6) WAF strategy: managed baseline + custom precision
A practical WAF approach balances broad managed protection and app-aware rule tuning.
Managed rule usage
- Start with baseline managed protections enabled
- Monitor initial detection/blocked events for noisy paths
- Tune exception handling narrowly and time-bound
Custom rule focus areas
- Sensitive admin/API routes
- High-risk methods on business-critical endpoints
- Known abuse patterns from prior incidents
- Country/ASN or traffic-profile controls where justified
Rule quality guidance
- Every custom rule should map to a clear abuse case
- Every exception should have owner, rationale, and expiry
- Every major rule change should have rollback plan
7) Rate limiting and abuse control patterns
Rate limits should reflect endpoint business sensitivity, not one global value.
Endpoint-specific model
| Endpoint Type | Risk Pattern | Practical Rate Strategy |
|---|---|---|
| Login/Auth | Credential stuffing, brute force | Tight thresholds + progressive challenge/temporary blocks |
| Password Reset | Account abuse and lockout manipulation | Strict limits with identity-aware guardrails |
| Search/Public Read | Scraping and resource pressure | Moderate limits with bot-aware controls |
| API Write/Mutation | Automated abuse and data integrity risk | Lower burst tolerance + strict per-client controls |
| Admin Panels | Unauthorized probing and high-risk actions | Very restrictive access + identity gates |
Rate limits should be reviewed after traffic growth, marketing events, or major product launches.
8) Cloudflare and origin hardening must work together
Edge controls reduce noise and first-contact risk. Origin controls enforce final trust decisions.
Origin controls to keep in place
- Application authentication and authorization checks
- Secure session handling and least-privilege app roles
- Host/network firewall restrictions
- Patch management and runtime hardening
- Secure secrets and key-management practices
Never treat edge controls as a substitute for secure origin architecture.
9) Logging, SIEM, and incident response integration
Cloudflare telemetry is most valuable when correlated with app, identity, and infrastructure logs.
Log integration priorities
- Export edge event data with reliable retention
- Normalize fields (client IP context, path, action, rule IDs)
- Build correlation with WAF, auth, and backend logs
- Add triage playbooks for common edge alert patterns
Practical IR handoff fields
| Field | Why IR Needs It |
|---|---|
| Timestamp (UTC) | Timeline integrity across systems |
| Host/Path/Method | Identifies targeted service behavior |
| Security Action Taken | Shows block/challenge/allow outcome |
| Rule Identifier | Maps event to control logic |
| Client Context | Supports source pattern analysis |
| Correlated Backend Signal | Distinguishes blocked noise from successful impact |
A blocked event is useful. A correlated blocked event is actionable.
10) Common Cloudflare mistakes in public app security
- Origin IPs still exposed after enabling proxy features
- Weak TLS mode choices for convenience
- No endpoint-specific rate limits on auth/API paths
- Admin panels left public without identity-based access
- WAF enabled without tuning and ownership
- Rule sprawl with unclear precedence and stale exceptions
- Logs available but not integrated into detection workflows
Fast anti-drift guardrails
- Monthly origin exposure verification
- Quarterly rule and exception review
- Continuous TLS posture checks after infra changes
- Alerting on high-risk config changes
11) Cloudflare public-app security checklist
| Control Area | Checklist Item | Done |
|---|---|---|
| DNS Governance | Stale records removed and ownership documented | ☐ |
| Origin Protection | Origin not directly reachable from public internet | ☐ |
| TLS Posture | HTTPS enforced and secure mode validated | ☐ |
| WAF Baseline | Managed protections enabled and monitored | ☐ |
| Custom Rules | Sensitive routes protected with app-aware logic | ☐ |
| Rate Limiting | Auth/API/admin endpoints have tailored limits | ☐ |
| Access Control | Admin surfaces protected with identity controls | ☐ |
| Logging | Edge/security logs exported and normalized | ☐ |
| SIEM Correlation | Edge events linked with backend/app telemetry | ☐ |
| Governance | Rule ownership, review cycle, and exception tracking active | ☐ |
12) 30-day implementation roadmap
Week 1: Visibility and baseline
- Inventory public DNS records and edge-protected routes
- Validate origin exposure status
- Establish initial risk register for top exposed endpoints
Output: public app exposure baseline report
Week 2: Core protection rollout
- Tighten TLS settings and HTTPS behavior
- Enable/tune managed WAF protections
- Add critical custom rules for high-risk routes
Output: core edge hardening change set
Week 3: Abuse controls and access hardening
- Implement endpoint-specific rate limits
- Protect admin interfaces with identity-based access concepts
- Validate bot-abuse handling on authentication paths
Output: abuse-control and access hardening report
Week 4: Detection and governance
- Complete log export and SIEM correlation workflows
- Define review cadence for rules, exceptions, and incidents
- Publish operational runbook for Cloudflare change management
Output: 30-day cloud edge security operating model
Cloudflare delivers the most security value when controls are tuned to real application behavior, origin hardening stays strong, and logs feed a living detection-and-response process.
Edge security operations worksheet
| Workstream | Owner | First Action | Validation Signal |
|---|---|---|---|
| DNS and origin governance | Platform owner | Audit DNS records and origin exposure paths | Reduced origin bypass opportunities |
| WAF tuning lifecycle | Security engineer | Review top blocked/challenged events weekly | Improved signal quality with fewer false positives |
| Rate-limit effectiveness | App + security team | Validate endpoint thresholds by business function | Lower abuse impact on auth/API paths |
| Log-to-IR integration | SOC lead | Correlate edge events with backend telemetry | Faster incident triage decisions |
Weekly checklist
- Verify origin IP protection remains effective
- Review high-volume attack patterns by route
- Update rule exceptions with owner and expiry
- Validate admin path access controls
Control governance and handoff pack
| Artifact | Minimum Content | Consumer |
|---|---|---|
| Edge control register | Rules, rate limits, owner, review date | Security + platform teams |
| Exception list | Rationale, risk, compensating controls, expiry | Risk/governance stakeholders |
| Detection summary | Top attack patterns and correlated outcomes | SOC/IR teams |
| Change report | Recent control updates and measured impact | Leadership + engineering owners |
Quality checks
- Are edge controls mapped to concrete abuse cases?
- Are exceptions temporary and justified by business need?
- Are backend and edge controls aligned for critical routes?
90-day edge hardening cadence
Days 1–30
- Baseline edge controls, origin exposure, and abuse patterns
- Close highest-risk misconfigurations (TLS, admin path, open origins)
- Create monthly control health scorecard
Days 31–60
- Tune WAF and rate-limit controls by endpoint sensitivity
- Improve log correlation with application and identity events
- Reduce false-positive exceptions through targeted rule refinement
Days 61–90
- Audit configuration drift and stale rule inventory
- Validate operational readiness with incident simulation scenario
- Publish next-quarter edge security roadmap
| KPI | Why It Matters |
|---|---|
| Origin bypass exposure count | Core edge-to-origin protection indicator |
| Actionable edge alert ratio | Detection quality measure |
| Auth/API abuse incident reduction | Practical risk outcome metric |
| Exception closure rate | Governance maturity signal |
Cloud edge security remains effective when control tuning, governance ownership, and incident visibility evolve together over time.
Cloudflare control tuning runbook (so changes stay safe)
Edge controls are powerful, but careless tuning can block real users. Treat WAF and rate-limiting changes like controlled releases.
Change checklist (before enabling)
- Identify the exact customer impact risk (what could be blocked).
- Start in a log/monitor mode where possible.
- Define rollback conditions (error spikes, conversion drops, support tickets).
- Confirm ownership: who watches dashboards during rollout.
Evidence you should capture per change
| Artifact | Why |
|---|---|
| Before/after traffic snapshot | Shows improvement and side effects |
| Top triggered rules | Identifies noisy or misfiring controls |
| Allowlist decisions | Prevents repeated “quick fixes” |
| Incident linkage | Connects tuning to real events |
Operational KPIs
| KPI | Target direction |
|---|---|
| WAF blocks leading to support tickets | Down |
| Confirmed attack traffic blocked | Up |
| Rate-limit false positives | Down |
| Time to rollback a bad change | Down |
This keeps Cloudflare security controls professional: measured tuning, controlled rollout, and clear ownership for outcomes.