IAM is the cloud control plane for identity, trust, and authorization decisions. Most cloud incidents that look like “network” or “application” problems eventually trace back to identity design problems: excessive permissions, weak trust boundaries, stale credentials, or poor separation of duties.
A practical IAM review does not start with exploitation thinking. It starts with visibility, ownership clarity, and least-privilege engineering that teams can maintain over time.
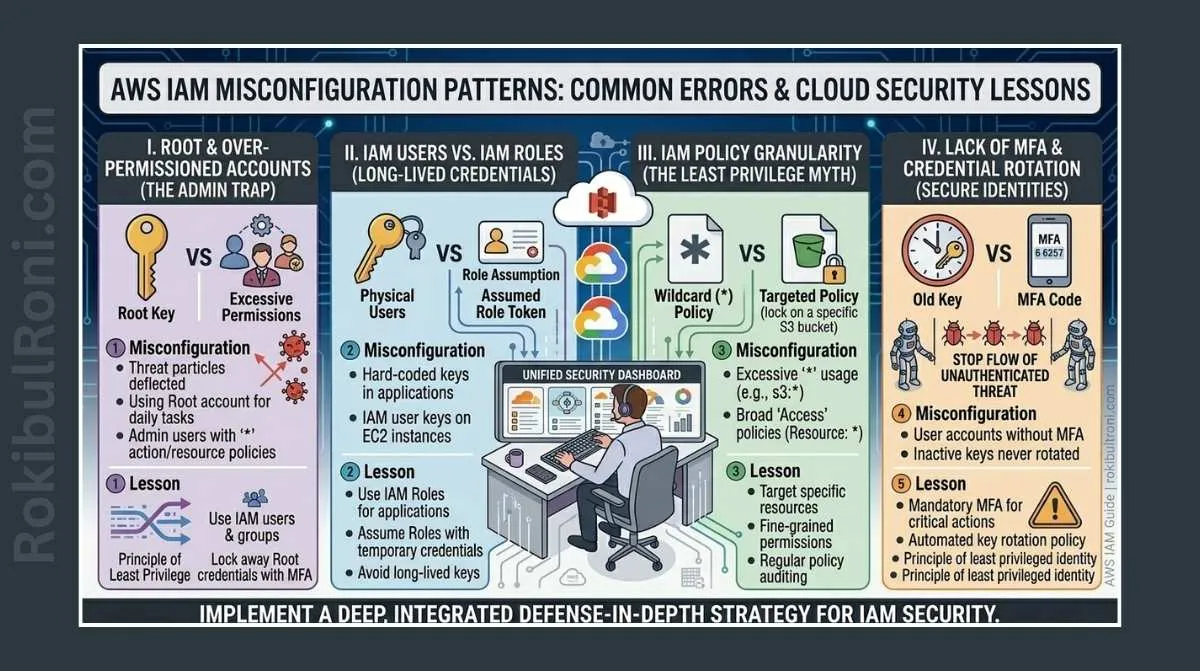
AWS IAM misconfiguration patterns
Use this as a defensive review framework for internal cloud security assessments and hardening projects.
1) Why IAM is the modern cloud perimeter
- API-level access is the real path to cloud control
- Misconfigured identities can bypass strong network controls
- Service-to-service trust mistakes create lateral movement risk
- Long-lived credentials increase breach blast radius
- IAM debt compounds quickly as cloud estates grow
If identity posture is weak, hardening only compute and network layers will not reduce overall risk enough.
2) Common IAM misconfiguration patterns and risk
| Misconfiguration | Risk | How to Detect | Remediation |
|---|---|---|---|
| Overly broad IAM policies | Unnecessary access to sensitive APIs/resources | Identify policies with large action/resource scope | Reduce permissions to task-specific actions and scoped resources |
Wildcard permissions (*) | Privilege expansion beyond intended use | Query for wildcard Action/Resource in attached policies | Replace with explicit allowlist and condition keys |
| Stale users and unused principals | Persistent dormant access paths | Compare last-used timestamps with ownership records | Disable, review, and remove unused identities |
| Long-lived access keys | Credential theft and replay risk window | Audit key age and usage patterns | Rotate keys, prefer temporary credentials and role-based access |
| Weak role trust policies | Unintended role assumption | Review trust relationships and principal scope | Restrict trust policy principals and add conditions |
| Missing MFA for sensitive access | Higher credential abuse risk | Check MFA enforcement on privileged console users | Enforce MFA policies for high-risk roles and break-glass paths |
| Excessive admin role spread | Elevated blast radius across accounts | Inventory AdministratorAccess and equivalent custom roles | Introduce tiered admin model and approval gating |
| Poor service account separation | Automation abuse and privilege confusion | Map workload identities to responsibilities | Split service roles by function and environment |
| Unmanaged cross-account access | Hidden trust pathways and governance gaps | Review external principals in trust policies and org boundaries | Govern cross-account roles with ownership, conditions, and review cycle |
This table should be treated as a recurring control review, not a one-time migration checklist.
3) Safe IAM review workflow (read-only first)
A strong IAM assessment starts with observation, inventory, and policy analysis before any change is applied.
Read-only review sequence
- Build identity inventory (users, groups, roles, policies, service-linked roles)
- Map ownership (team, application, environment, business criticality)
- Analyze attached and inline policies for excess scope
- Review trust policies for role assumption boundaries
- Inspect credential hygiene (key age, MFA posture, unused principals)
- Validate cross-account and federated access paths
- Prioritize remediation by exposure and business impact
Review output structure
| Output | Purpose |
|---|---|
| Identity inventory map | Understand who/what can access which resources |
| Permission risk register | Prioritized list of high-risk permission patterns |
| Trust relationship map | Visualize assumption pathways across accounts/services |
| Remediation backlog | Assignable tasks with owner and target date |
Start read-only, collect evidence, then change deliberately with rollback plans.
4) Practical policy analysis principles
Policy tuning is where many teams overcorrect. The goal is least privilege without breaking delivery.
Policy review checks
- Remove unused actions tied to legacy workflows
- Scope
Resourcevalues wherever technically possible - Add condition keys for stronger context checks
- Separate human-admin and workload-automation permissions
- Avoid embedding broad permissions in reusable base roles
High-value analysis questions
- Which permissions are rarely used but highly risky?
- Which roles are shared across unrelated workloads?
- Which policies include broad write/delete actions in production?
- Which trust policies permit unnecessary external assumption?
5) Logging and monitoring for IAM risk visibility
IAM hardening is incomplete without detection and continuous review.
Core monitoring components
- CloudTrail for IAM and control-plane event visibility
- GuardDuty concept for suspicious access behavior signals
- AWS Config concept for drift and policy compliance checks
- SIEM integration for correlation across identity, endpoint, and network telemetry
IAM monitoring table
| Control | What to Monitor | Practical Signal |
|---|---|---|
| Identity Lifecycle | User/role creation, permission changes | Unexpected privilege grants outside change windows |
| Credential Hygiene | Key creation/rotation/use patterns | Stale keys and unusual usage spikes |
| Trust Boundaries | Role assumption across accounts | New or unusual cross-account assume-role events |
| Privilege Escalation Signals | Policy attachment/inline edits to privileged principals | Rapid permission expansion on sensitive roles |
| Detection Coverage | Alert fidelity and triage outcomes | Repeated false positives or missed escalation events |
Log retention and normalization matter as much as alert rules.
6) How IAM mistakes affect core AWS services
IAM misconfiguration impact is service-specific. Make that visible in reports.
| Service Area | IAM Weakness Pattern | Potential Business Effect |
|---|---|---|
| CI/CD Pipelines | Overprivileged deployment roles | Unauthorized release changes or environment drift |
| S3 Data Stores | Broad read/write policies | Data exposure, integrity loss, or accidental deletion |
| EC2 Workloads | Weak instance profile controls | Host-level actions beyond workload intent |
| Lambda Functions | Shared high-privilege execution roles | Function misuse and cross-service access spread |
| Kubernetes (EKS) | Overbroad IAM-to-workload mappings | Namespace boundary weakening and secret access risk |
Mapping by service helps engineering teams prioritize remediation where impact is highest.
7) Least-privilege rollout strategy that teams can sustain
Least privilege fails when implemented as a one-time policy rewrite with no operating model.
Phased rollout model
- Discovery phase
- Inventory identities, permissions, and owners.
- Risk reduction phase
- Remove obvious broad grants and stale identities.
- Policy refinement phase
- Tighten permissions by role purpose and environment.
- Guardrail phase
- Add policy checks in CI/CD and infrastructure workflows.
- Continuous review phase
- Reassess access patterns monthly/quarterly.
Least-privilege governance table
| Governance Control | Frequency | Owner |
|---|---|---|
| Privileged role review | Monthly | Cloud security lead |
| Stale identity cleanup | Monthly | IAM operations owner |
| Cross-account trust audit | Quarterly | Cloud platform team |
| Policy drift/compliance review | Weekly/bi-weekly | DevSecOps + platform engineering |
| Break-glass access test | Quarterly | Security operations |
8) Common mistakes during IAM remediation
- Removing permissions without dependency mapping, causing outages
- Converting wildcards too aggressively without role testing
- Leaving cross-account trust relationships undocumented
- Enforcing MFA inconsistently across privileged pathways
- Keeping shared “temporary” admin roles permanently
- Failing to assign ownership for policy maintenance
- Treating IAM review as a yearly audit-only activity
Practical anti-pattern guardrails
- Every permission change must have owner + rollback plan
- Every trust policy change must include impact review
- Every admin-equivalent role requires documented business justification
- Every remediation item needs retest evidence before closure
9) AWS IAM review checklist (reusable)
| Review Area | Checklist Item | Done |
|---|---|---|
| Identity Inventory | Users, roles, groups, and policies inventoried with owners | ☐ |
| Privilege Scope | Wildcards and broad grants identified and prioritized | ☐ |
| Credential Security | MFA posture and key hygiene reviewed | ☐ |
| Trust Policies | Cross-account and federated trust paths validated | ☐ |
| Service Roles | Workload roles separated by purpose and environment | ☐ |
| Monitoring | CloudTrail/Config/GuardDuty signals reviewed | ☐ |
| SIEM Correlation | IAM events integrated and triaged with context | ☐ |
| Remediation Tracking | Tasks assigned with due dates and owners | ☐ |
| Retest Status | High-risk fixes validated and documented | ☐ |
10) Operational metrics for IAM hardening progress
| Metric | Why It Matters | Desired Direction |
|---|---|---|
| % identities with admin-equivalent access | Indicates concentration of high-risk privilege | Down |
| % policies with wildcard actions/resources | Measures overbroad policy posture | Down |
| Avg age of active access keys | Proxy for credential hygiene maturity | Down |
| MFA coverage on privileged identities | Core protection against credential abuse | Up |
| Cross-account trust relationships with owner tags | Governance quality indicator | Up |
| IAM-related incident/near-miss count | Outcome signal for hardening effectiveness | Down over time |
A mature IAM program is iterative and operational: clear ownership, safe read-only assessments, measured privilege reduction, and continuous monitoring that catches drift before it becomes incident-level risk.
11) Change-safe IAM remediation sequence
Permission cleanup can break production workflows if implemented without sequence discipline.
Safer remediation order
- Identify highest-risk overprivileged identities.
- Simulate narrowed permissions in non-production or controlled test windows.
- Apply scoped changes in phases, starting with least critical workloads.
- Monitor CloudTrail and application health after each phase.
- Roll forward only when no critical breakage appears.
| Phase | Goal | Exit Criteria |
|---|---|---|
| Phase 1 | Reduce obvious wildcard and stale access | No service-impacting auth failures |
| Phase 2 | Tighten trust policies and cross-account assumptions | Expected role assumptions only |
| Phase 3 | Enforce stronger identity controls (MFA/key hygiene) | Privileged access paths validated |
12) Cross-account IAM governance model
As cloud estates grow, unmanaged cross-account access becomes one of the hardest risks to track.
| Governance Control | Practical Requirement |
|---|---|
| Ownership tagging | Every cross-account role has clear service/team owner |
| Purpose documentation | Trust relationship includes business justification |
| Review cadence | Quarterly review of external principals and conditions |
| Exception handling | Time-bound approvals with compensating controls |
Cross-account IAM stays secure when trust relationships are treated as living governance objects, not static configuration entries.
IAM operations worksheet for cloud teams
| Workstream | Owner | First Action | Validation Signal |
|---|---|---|---|
| Inventory governance | Cloud security lead | Maintain identity and policy ownership map | Fewer unmanaged IAM objects over time |
| Privilege reduction | IAM engineer | Prioritize high-risk wildcard and admin-equivalent paths | Measurable drop in excessive privilege exposure |
| Trust boundary control | Platform owner | Review cross-account trust conditions quarterly | Fewer undocumented trust relationships |
| Monitoring assurance | SOC + cloud ops | Validate IAM telemetry in SIEM workflows | Faster detection of risky permission changes |
Weekly governance checklist
- Review high-risk IAM changes from CloudTrail events
- Validate owner tags on new roles and policies
- Track stale keys and inactive identities for cleanup
- Ensure exceptions have expiration and compensating controls
Change-control and rollback pack
| Artifact | Minimum Content | Consumer |
|---|---|---|
| Change request | Policy/trust updates with risk rationale | Platform + security reviewers |
| Impact map | Workloads/services affected by permission changes | Engineering teams |
| Rollback plan | Previous state and emergency restore approach | Operations/on-call |
| Validation report | Post-change checks and anomaly observations | Security governance |
Quality checks
- Were permission changes validated against service behavior?
- Is rollback path documented and tested for critical roles?
- Are logging/detection controls confirming expected behavior?
90-day IAM hardening cadence
Days 1–30
- Baseline privileged identities and wildcard policy usage
- Execute first high-risk cleanup wave with rollback safeguards
- Publish IAM risk dashboard for stakeholders
Days 31–60
- Tighten cross-account trust relationships and owner tagging
- Improve key hygiene and privileged MFA coverage
- Link IAM findings with incident and vulnerability trends
Days 61–90
- Conduct quarterly access review and exception audit
- Validate sustained privilege reduction without service breakage
- Publish next-quarter IAM hardening priorities
| KPI | Why It Matters |
|---|---|
| Admin-equivalent identity count | Tracks privilege concentration risk |
| Wildcard policy prevalence | Measures policy quality maturity |
| Cross-account trust with owner metadata | Indicates governance discipline |
| IAM-related incident indicators | Reflects control effectiveness |
IAM programs become durable when reduction, detection, and governance practices are maintained continuously rather than only during audit windows.
IAM remediation operating model (what to standardize)
Most IAM misconfigurations persist because teams don’t have a consistent way to review, approve, and measure permission changes.
1) Permission review checklist (per role)
- What workload uses this role (service name, environment)?
- Is there a permission boundary or other guardrail?
- Are actions scoped to specific resources (ARNs) rather than
*? - Are any admin-like actions present (IAM, KMS, STS) and are they required?
- Is there a documented owner and rotation/expiry plan?
2) Exceptions policy
If you must keep broad permissions temporarily:
- Put an expiry date on the exception.
- Track it like technical debt (ticket + owner).
- Require a compensating control (monitoring, alerts, approval workflows).
3) Detection hooks to maintain
- Alerts for policy changes to high-privilege roles.
- Alerts for unusual role assumption patterns.
- Continuous evaluation findings triaged with ownership.
4) KPIs that map to real reduction
| KPI | Target direction |
|---|---|
| Roles with wildcard actions/resources | Down |
| Unowned roles/policies | Down to zero |
| Exceptions past expiry | Down to zero |
| Time-to-fix critical IAM findings | Down |
This makes IAM work professional: explicit ownership, measured reduction, and controlled exceptions rather than permanent over-permission.