A strong cybersecurity career in Malaysia is built on visible capability, not just certificates. Employers and teams want proof that you can solve real technical problems, document findings clearly, and work reliably in operations.
The fastest path is usually fundamentals + lab evidence + communication quality. When those three grow together, your portfolio becomes credible even before your first full-time security title.
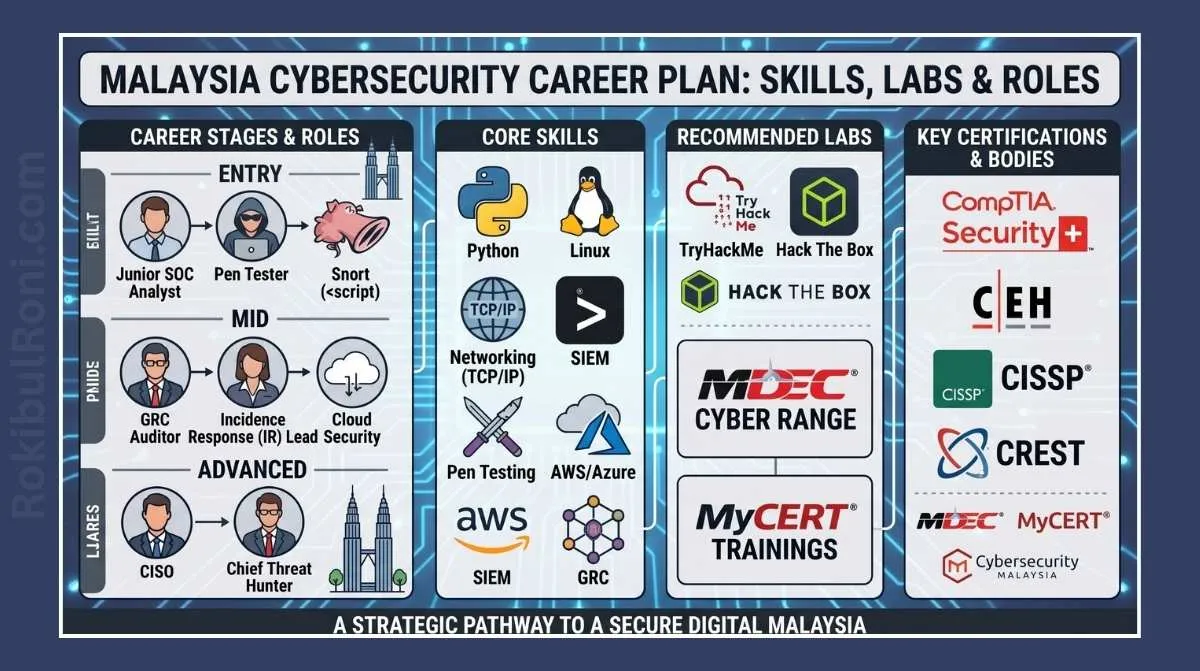
Malaysia cybersecurity career plan
Use this guide as a practical roadmap for students, fresh graduates, and career switchers in Malaysia.
1) Why fundamentals and portfolio evidence matter
- Security work depends on networking, systems, and troubleshooting basics
- Labs turn theory into demonstrable technical skill
- Writing and reporting show professional readiness
- Employers trust practical evidence more than keyword-heavy resumes
- A structured learning path prevents tool-chasing and burnout
A practical portfolio can outperform generic credential lists in interview discussions.
2) Role paths to choose from early
You do not need to decide your final specialization on day one, but you should pick an initial path for focused learning.
| Role Path | Core Focus | Typical Early Responsibilities |
|---|---|---|
| SOC Analyst | Monitoring, triage, incident detection | Alert review, log analysis, escalation |
| Penetration Tester | Authorized offensive assessment | Recon, validation, findings reporting |
| Cloud Security Analyst | Cloud IAM/configuration posture | Baseline reviews, hardening checks, logging validation |
| GRC Analyst | Policies, controls, risk governance | Control mapping, audit support, documentation |
| Incident Responder | Investigation and containment workflows | Timeline building, evidence handling, response coordination |
| Vulnerability Analyst | Risk prioritization and remediation tracking | Scan validation, prioritization, retest follow-up |
How to pick your starting path
- If you enjoy live operations and telemetry, start SOC.
- If you enjoy testing and technical validation, start pentesting/AppSec track.
- If you like architecture and governance, start cloud security or GRC.
Your first role is a starting point, not a permanent label.
3) Foundation skills every path needs
No matter which role you choose, these fundamentals remain critical.
Core technical foundations
- Networking: TCP/IP, DNS, routing, common ports/protocol behavior
- Linux basics: shell usage, services, file permissions, logs
- Windows basics: event logs, processes, account controls
- Cloud basics: IAM, storage, networking, audit logs
- Scripting: Python/Bash for automation and parsing tasks
- Security concepts: CIA, access control, threat models, risk prioritization
Professional foundations
- Structured problem solving
- Clear written communication
- Collaboration with IT, developers, and non-security stakeholders
- Time management and learning discipline
Foundation maturity table
| Skill Domain | Beginner Milestone | Job-Ready Milestone |
|---|---|---|
| Networking | Identify protocol behavior and basic troubleshooting | Analyze suspicious traffic patterns with context |
| Linux/Windows | Navigate systems and read core logs | Perform repeatable host-level analysis workflows |
| Cloud | Understand service model and IAM basics | Run baseline security review and document findings |
| Scripting | Write small utility scripts | Automate repetitive security validation tasks |
| Communication | Explain findings in plain language | Deliver actionable technical reports |
4) Lab path that builds real capability
Lab progression should mirror security workflows used in real teams.
Recommended lab sequence
- Home fundamentals lab (network + OS operations)
- SIEM/detection lab (logs and alert triage)
- Web pentest lab (auth, access control, app behavior)
- Cloud baseline lab (IAM + logging + storage controls)
- Forensics lab (artifact and timeline analysis)
Lab path table
| Lab Stage | Main Objective | Portfolio Artifact |
|---|---|---|
| Home Lab | Build core system/network confidence | Setup diagram + operations checklist |
| SIEM Lab | Understand detection and triage flow | Alert triage notes + mini incident timeline |
| Web Pentest Lab | Practice safe testing and reporting | Findings report with remediation |
| Cloud Baseline Lab | Practice defensive cloud hardening | Baseline checklist + gap register |
| Forensics Lab | Build evidence-handling discipline | Investigation summary and artifact map |
Lab evidence should be reproducible, safe, and clearly documented.
5) Tool map for practical learning
Use tools to support workflow, not to replace thinking.
| Tool | Learning Use Case | Career Benefit |
|---|---|---|
| Nmap | Service discovery and exposure validation | Strong recon and network context |
| Wireshark | Packet-level troubleshooting and triage | Better incident and network analysis |
| Burp Suite | Web/API request analysis and safe validation | Essential app security workflow skill |
| Nessus / OpenVAS | Vulnerability baseline and prioritization practice | Vulnerability management readiness |
| Splunk / ELK / Wazuh | Detection, triage, and investigation workflow | SOC and IR capability building |
| Autopsy | Forensic artifact review and timeline practice | Incident and forensics support skill |
| Git / GitHub | Portfolio publishing and script versioning | Professional collaboration and visibility |
| Python / Bash | Automation and parsing tasks | Operational efficiency and repeatability |
Do not try to master everything at once. Depth beats breadth in early stages.
6) 12-month cybersecurity roadmap (Malaysia-focused, practical)
This plan is designed for part-time learners and early professionals.
Quarter 1 (Months 1–3): Build foundations + first artifacts
- Study networking, Linux/Windows basics, security fundamentals
- Build home lab and document architecture
- Start basic scripting exercises
- Publish first technical note/writeup
Output: foundational lab + first portfolio artifact
Quarter 2 (Months 4–6): Specialization starter track
- Choose primary path (SOC / pentest / cloud / IR)
- Run 2–3 guided labs aligned to chosen path
- Build one structured report (incident or pentest style)
Output: role-aligned mini project portfolio
Quarter 3 (Months 7–9): Operational depth
- Add cross-functional skills (e.g., SOC + web security, pentest + reporting)
- Improve evidence quality and communication format
- Contribute scripts or templates to GitHub
Output: advanced case study with clear workflow and outcomes
Quarter 4 (Months 10–12): Career transition readiness
- Refine CV and portfolio for target role
- Practice interview narratives with real project examples
- Apply strategically to internship/junior/transition roles
Output: job-ready portfolio pack + targeted application pipeline
7) Portfolio strategy that hiring teams can trust
Portfolio should show method, not just screenshots.
High-value portfolio elements
- Blog posts explaining technical workflow and decisions
- Redacted case-study writeups with evidence and remediation
- GitHub scripts solving practical security tasks
- Lab diagrams and architecture notes
- Detection notes or pentest reports using safe dummy targets
Portfolio quality table
| Item | Strong Version | Weak Version |
|---|---|---|
| Blog Post | Workflow-focused, practical, and reproducible | Generic theory summary |
| GitHub Repo | Clean README, purpose, usage, output examples | Script dump without context |
| Lab Report | Scope, method, evidence, remediation, lessons | Screenshots only |
| Career Narrative | Shows growth path and role alignment | Vague motivation statements |
A smaller high-quality portfolio is better than a large unfocused one.
8) Soft skills that accelerate growth
Technical skill gets interviews; communication and reliability often decide offers.
Must-build soft skills
- Clear technical writing
- Team collaboration across non-security stakeholders
- Adaptability under changing priorities
- Structured troubleshooting communication
- Professional accountability and follow-through
Practical soft-skill drills
- Write one-page technical summaries after each lab
- Explain one technical concept weekly in plain language
- Practice “what happened / why it matters / what next” brief format
9) Common mistakes to avoid
- Collecting certificates without hands-on lab depth
- Ignoring Linux and networking fundamentals
- Chasing too many tools in parallel
- Publishing weak portfolio items without technical substance
- Skipping report writing and communication practice
- Applying for roles without role-specific evidence
Fast guardrails
- Every month must produce at least one portfolio artifact
- Every lab should end with a short written report
- Every quarter should include one deeper role-aligned project
10) Next-week action plan (practical and immediate)
If you are starting now, use this one-week plan to build momentum.
| Day | Action | Output |
|---|---|---|
| Day 1 | Choose target role path and skill gaps | Personal roadmap draft |
| Day 2 | Set up lab environment (VM/container + notes) | Lab setup documentation |
| Day 3 | Complete one focused technical exercise | Exercise notes + screenshots |
| Day 4 | Write short technical report from exercise | First writeup draft |
| Day 5 | Push one script/note to GitHub with README | Public portfolio item |
| Day 6 | Review job descriptions for target role and map missing skills | Skill-gap tracker |
| Day 7 | Plan next 30 days with 2 labs + 1 writeup milestone | 30-day action board |
Momentum matters more than perfection in the first month.
11) Career growth checkpoints for the first year
| Checkpoint | Month Target | Success Signal |
|---|---|---|
| Foundation Confidence | Month 3 | Can explain and troubleshoot core network/system behavior |
| First Role-Ready Project | Month 6 | Portfolio includes one complete case-style project |
| Cross-Functional Strength | Month 9 | Can connect detection, testing, and reporting workflows |
| Transition Readiness | Month 12 | Role-aligned CV + portfolio + interview examples prepared |
A practical cybersecurity career plan in Malaysia does not require perfect timing or expensive tooling. It requires disciplined fundamentals, safe lab practice, visible portfolio evidence, and consistent communication growth that proves you can deliver value in real security teams.
Career operations worksheet (Malaysia context)
| Workstream | Owner | First Action | Validation Signal |
|---|---|---|---|
| Role targeting | You | Select one primary and one secondary role path | Focused learning and portfolio alignment |
| Lab execution discipline | You | Run scheduled weekly labs with documented outputs | Steady build-up of practical artifacts |
| Portfolio visibility | You | Publish monthly writeup/script/case study | Stronger evidence in applications/interviews |
| Communication growth | You | Practice technical summaries for mixed audiences | Better interview and workplace readiness |
Monthly checklist
- Review roadmap and adjust based on progress reality
- Improve one older artifact for quality, not just quantity
- Map new learning to target job descriptions
- Track soft-skill growth alongside technical milestones
Career evidence handoff pack
| Artifact | Minimum Content | Consumer |
|---|---|---|
| Role-aligned CV | Skills, projects, outcomes linked to target role | Hiring teams |
| Portfolio index | Organized links with project summaries | Recruiters/interviewers |
| Technical case studies | Scope, method, evidence, and lessons | Technical interviewers |
| Learning tracker | Monthly progress and gap closure history | Mentors and self-review |
Quality checks
- Does each artifact show method and outcome, not only tool names?
- Can you explain each portfolio item clearly in interviews?
- Are project writeups improving in depth and structure?
90-day practical growth cadence
Days 1–30
- Finalize role target and skill-gap matrix
- Complete two focused labs and one publishable writeup
- Improve baseline networking/Linux/cloud fundamentals
Days 31–60
- Build one deeper specialization project (SOC/pentest/cloud/IR)
- Add script or template artifact to GitHub with clean README
- Practice interview stories from real project outcomes
Days 61–90
- Refine CV and portfolio for role-specific applications
- Run mock interviews and address recurring weak areas
- Apply strategically and track response patterns
| KPI | Why It Matters |
|---|---|
| Monthly artifact production | Measures execution consistency |
| Role-fit project ratio | Shows portfolio relevance |
| Interview feedback improvement | Indicates communication maturity |
| Skill-gap closure rate | Reflects practical learning progress |
Career growth becomes more predictable when learning, evidence, and communication are tracked as one integrated system rather than separate efforts.
90-day execution plan (turn the plan into real evidence)
A career plan is only credible when it produces portfolio artifacts, not just study hours.
Days 1–30: foundation and positioning
- Choose a target track (SOC, cloud security, appsec, GRC) and write a one-paragraph “why.”
- Build a baseline lab and documentation habit.
- Publish one short technical note each week (what you learned + proof).
Days 31–60: specialization and proof
- Complete one focused project (e.g., detection rule set, cloud baseline notes, app testing workflow).
- Write one professional case study-style post: problem → approach → outcomes.
- Ask for feedback from practitioners (community groups, peers, mentors).
Days 61–90: interview readiness
- Prepare 5 “story” examples (incident handled, control improved, investigation performed).
- Create a portfolio index page: projects, write-ups, and links.
- Practice explaining work clearly: impact, trade-offs, limitations.
This keeps the career article professional and relevant: measurable outputs, portfolio evidence, and a short-cycle plan that creates real momentum.