
Red Team Readiness Assessment
A strategic evaluation service that determines whether an organization can safely run, detect, and learn from full-scope adversary simulations mapped to the MITRE ATT&CK framework.
Deep analysis and reviews of the weapons, platforms, and defensive tools used in professional offensive security.

A strategic evaluation service that determines whether an organization can safely run, detect, and learn from full-scope adversary simulations mapped to the MITRE ATT&CK framework.
A comprehensive security review designed to harden GitHub Actions workflows, lock down secrets, restrict token permissions, mitigate dependency risks, and secure deployment gates.

A specialized service that designs, tunes, and validates SIEM detections across Splunk and Elastic/ELK, transforming raw log data into high-fidelity alerts for threat hunting and incident response.

A structured governance framework that transforms overwhelming vulnerability scan data into measurable remediation outcomes using asset context, exploitability metrics, and repeatable engineering workflows.

A structured, evidence-based web and API penetration testing program combining manual exploitation, automated validation, CVSS-based reporting, and developer-centric remediation guidance.
A profound, realistic look inside a high-stakes banking penetration test. This narrative bridges the gap between raw technical execution and strategic risk, showing exactly how an operator executes payloads and translates them into C-level business impact when a single misstep could disrupt a multi-billion dollar infrastructure.
A profound, high-octane narrative detailing a multi-cloud Red Team engagement for a financial entity. From breaking into GitLab pipelines to exploiting Kubernetes namespaces and chaining IAM roles for an AWS account takeover, this article maps the elite mindset required to conquer and secure modern cloud infrastructure.
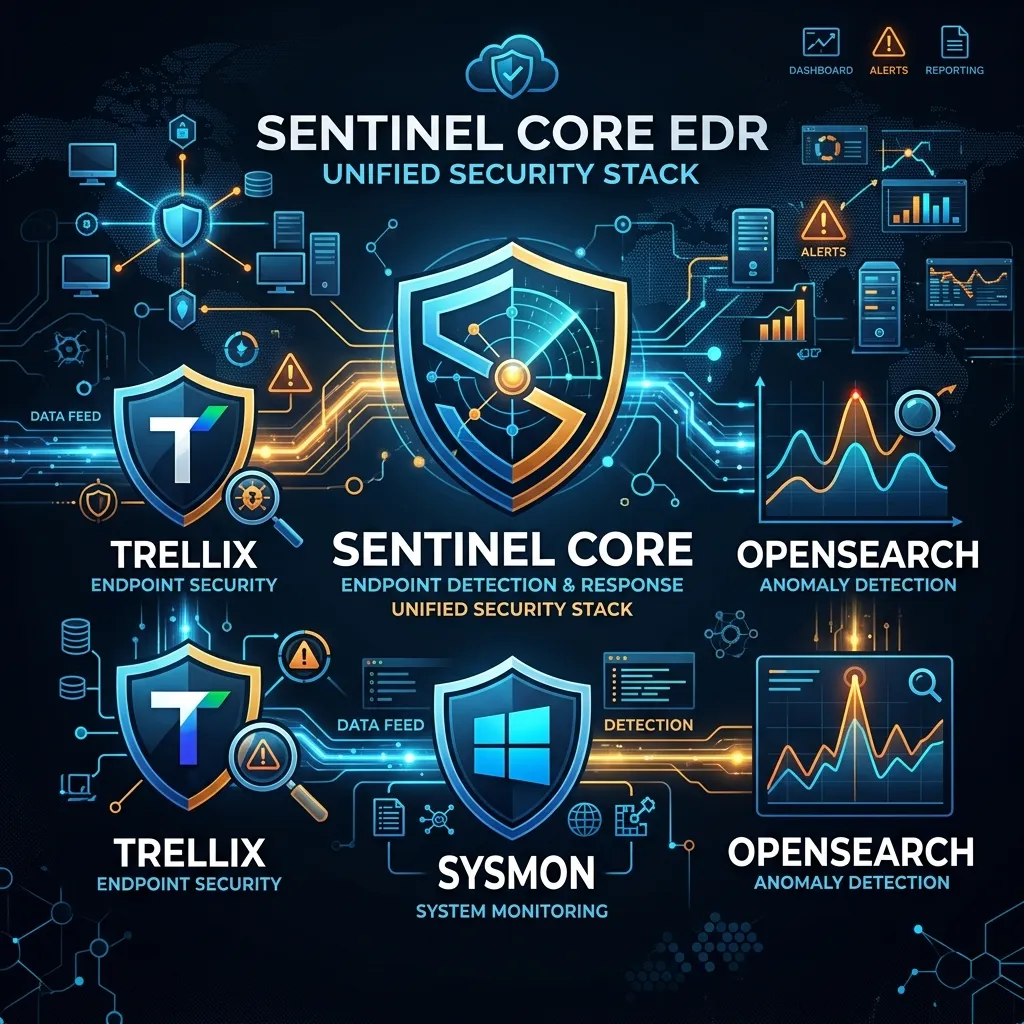
A practical, streamlined guide to building a hybrid Endpoint Detection and Response (EDR) capability. By layering Microsoft Sysmon's granular process telemetry beneath Trellix Endpoint Security, and feeding both into OpenSearch Anomaly Detection, SOC teams can achieve defense-in-depth, catching fileless malware and living-off-the-land (LotL) attacks with minimal engineering overhead.
A high-signal, tactical narrative detailing a real-world Red Team engagement under strict time constraints. This is not a tutorial. It bridges the gap between raw enumeration and attacker logic, demonstrating exactly how a professional operator uses Nmap as a decision engine to find actionable entry points when automated scanners fail.
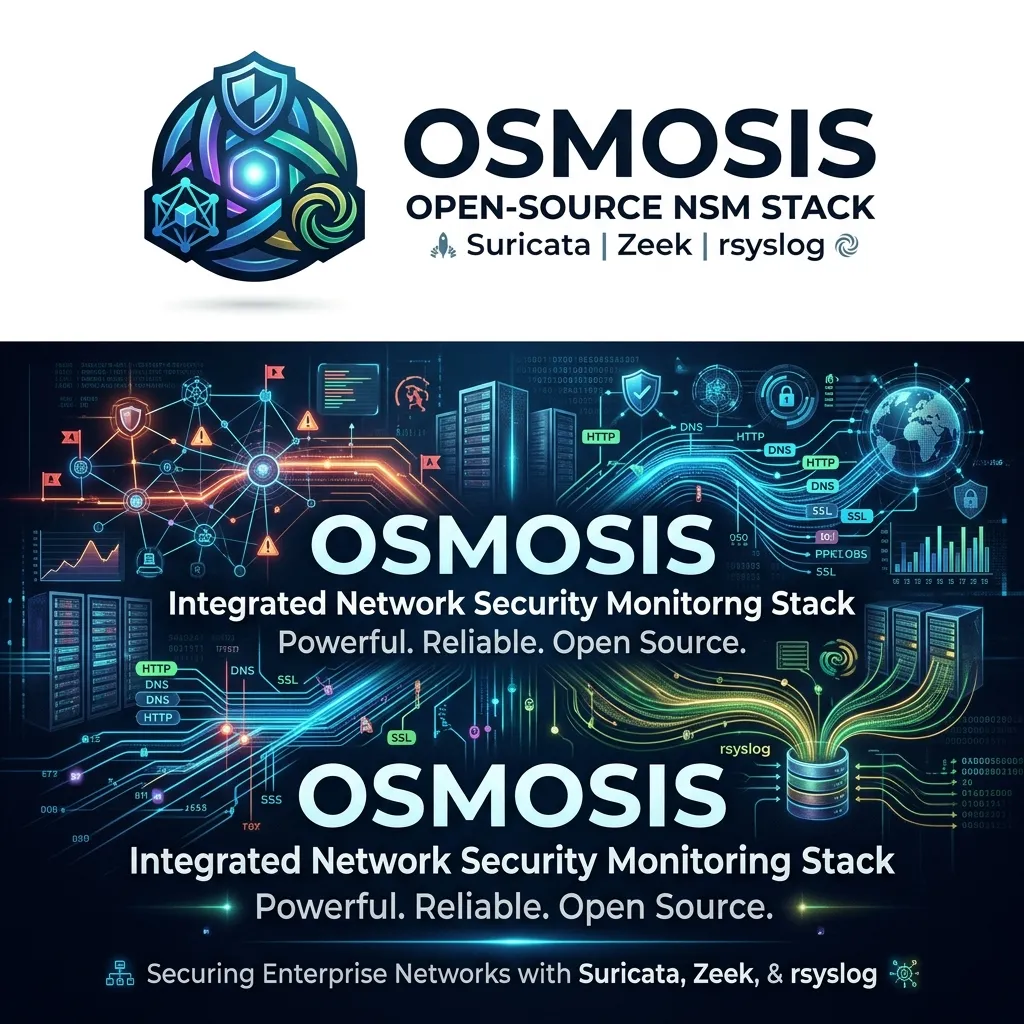
A comprehensive guide to architecting a production-grade Network Security Monitoring (NSM) stack using Suricata, Zeek, and rsyslog. This setup provides deep packet inspection, signature-based IDS/IPS, protocol metadata extraction, and reliable log routing. Essential for SOCs requiring total network visibility and wire-speed threat detection without commercial licensing constraints.

Receive my case study and the latest articles on my WhatsApp Channel.