During active incidents, logs tell you what systems claim happened. Packets show what actually moved across the wire. That difference is why packet analysis can decide whether a case is a real compromise, misconfiguration, or alert noise.
Wireshark is most useful when used as an evidence workflow, not a random packet viewer. The value comes from disciplined handling, correlation, and clear triage decisions.
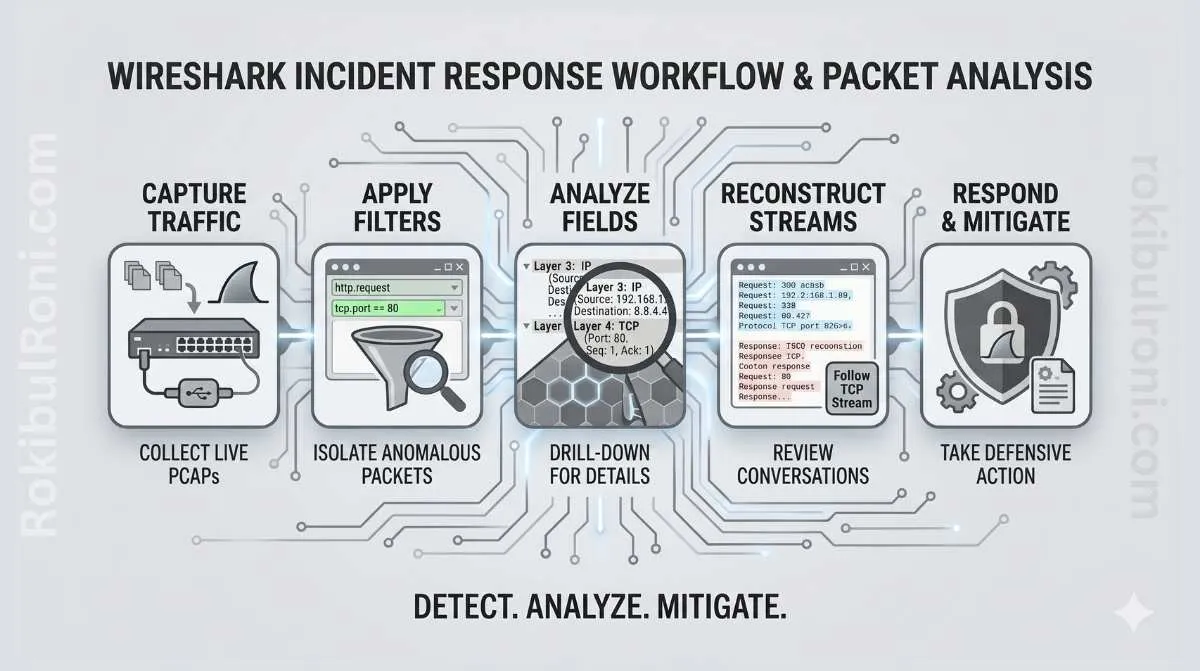
Wireshark incident response workflow
Use this structure for defensive, investigation-focused packet analysis in authorized environments.
1) Why packet evidence matters in incident response
- Validates suspicious events seen in SIEM or EDR timelines
- Reveals protocol-level behavior not captured in high-level logs
- Confirms source, destination, sequence, and timing of traffic
- Helps distinguish scanning noise from meaningful compromise indicators
- Supports defensible reporting and post-incident lessons
Packet evidence is strongest when combined with endpoint, authentication, and firewall telemetry.
2) When packet analysis helps and when logs are better
Use the right source for the question you are answering.
| Investigation Question | Best Starting Source | Why |
|---|---|---|
| Was there suspicious outbound communication? | PCAP + firewall logs | Packets confirm protocol/flow details while firewall gives policy context |
| Did a user account fail/succeed unusually? | Identity/auth logs first | Identity systems provide direct account activity detail |
| Was data transferred externally? | PCAP + proxy logs + endpoint telemetry | Packets reveal transfer behavior, logs add user/process context |
| Is this endpoint scanning or normal service checks? | PCAP first | Traffic pattern and timing expose reconnaissance behavior clearly |
| Did a web/API route receive malformed or abusive requests? | Web logs + WAF + selective packet review | App logs show semantic context, packets validate raw request patterns |
Practical rule: start with logs for broad triage, then use packets to confirm critical unknowns.
3) PCAP handling basics before opening Wireshark
Poor evidence handling can invalidate an otherwise good investigation.
PCAP preservation checklist
- Preserve original PCAP as read-only evidence
- Record collection source, tool, and capture interface
- Hash evidence file (e.g., SHA-256) and store hash record
- Document timezone and timestamp normalization method
- Use case ID and chain-of-custody log for transfers
- Redact sensitive data in shared exports, not in originals
Chain-of-custody table
| Field | What to Record |
|---|---|
| Case ID | Unique incident identifier |
| Evidence ID | PCAP file reference and storage path |
| Collected By | Name, role, and collection timestamp |
| Source | Sensor, TAP, host, or capture point |
| Integrity Hash | SHA-256 (or approved standard) value |
| Access Log | Who accessed evidence and when |
| Transfer Notes | Storage moves and access approvals |
Without this discipline, packet findings become hard to defend in audits or legal review.
4) Step-by-step Wireshark triage workflow
This flow keeps analysis focused and repeatable.
Step 1: Open and profile the capture
- Confirm capture timeframe and packet count
- Identify top talkers (source/destination)
- Review protocol distribution for anomalies
- Flag unusual spikes in traffic volume or session count
Step 2: Identify conversations and sessions
- Use conversation/endpoints views to identify dominant flows
- Group suspicious flows by protocol and destination
- Prioritize external destinations with unusual behavior
Step 3: Review protocol behavior
- Inspect DNS requests and response patterns
- Review HTTP metadata and request path anomalies
- Inspect TLS metadata (SNI, cert hints, handshake behavior)
- Review uncommon ports for protocol mismatch indicators
Step 4: Correlate with other telemetry
- Align packet timestamps with firewall events
- Map source hosts to endpoint telemetry/process data
- Validate auth events around suspicious network activity
Step 5: Document findings and next actions
- Capture evidence snippets with timestamps
- Record confidence level and hypothesis status
- Propose containment or deeper forensic actions
5) Useful Wireshark views and filters (defensive level)
Use filters to reduce noise while keeping context.
| Goal | Conceptual Filter Example | What It Helps You See |
|---|---|---|
| DNS triage | dns | Domain lookups, query frequency, suspicious naming patterns |
| Web request review | http | Request methods, paths, response codes, host behavior |
| TLS metadata review | tls | Handshake patterns, SNI usage, cert-related context |
| Traffic from one host | ip.addr == <host_ip> | Host-centric network behavior timeline |
| External destination focus | !(ip.addr == internal_ranges) style logic | Outbound communication candidates |
| Error/retransmission review | TCP analysis views | Potential instability, session anomalies, packet quality issues |
Keep filter use case-driven. Over-filtering too early can hide relevant context.
6) Triage table for investigation consistency
Use this table format in each incident case.
| Question | Where to Look | Evidence | Next Step |
|---|---|---|---|
| Is there suspicious outbound communication? | Conversations + external destination flows | Session timeline, destination profile, byte counts | Correlate with endpoint process and firewall policy |
| Did DNS behavior deviate from baseline? | DNS query/response patterns | Query volume anomalies, rare domain patterns | Check endpoint timeline and threat intel context |
| Is there potential data transfer anomaly? | Long sessions, large payload flows, repeated external posts | Flow duration and transfer metadata | Validate against approved app behavior and owner input |
| Are there signs of unauthorized service discovery? | Port/protocol scans and connection bursts | Sequential connection attempts and host targeting pattern | Segment source host and run endpoint triage |
| Is encrypted traffic limiting visibility? | TLS sessions with limited payload visibility | Metadata-only visibility notes | Use proxy/firewall/endpoint logs for complementary context |
7) Incident scenarios and packet-analysis approach
These scenarios keep analysis practical and defensive.
Scenario A: suspicious outbound connection
- Confirm host and user context from SIEM/EDR
- Review destination reputation and historical baseline
- Check flow timing relative to process execution events
- Classify as known service, misconfiguration, or potential compromise
Scenario B: possible data exfiltration indicator
- Review session size, timing, and recurrence patterns
- Compare destination with approved business integrations
- Correlate with file access logs and endpoint activity
- Escalate if evidence supports unauthorized transfer hypothesis
Scenario C: potential malware callback indicator
- Identify recurring beacon-like periodic connections
- Compare protocol behavior to normal host baseline
- Check endpoint detections and startup persistence evidence
- Isolate host if confidence increases after correlation
Scenario D: DNS anomaly
- Track high-volume or rare-domain query behavior
- Compare TTL behavior and resolution stability
- Correlate with user/session changes and outbound sessions
- Escalate if pattern aligns with malicious staging behavior
Scenario E: unauthorized service discovery pattern
- Review connection attempts across many ports/hosts in short windows
- Validate if source is approved scanner or admin tooling
- Confirm change ticket or scheduled scan context
- Trigger containment if unapproved reconnaissance is confirmed
8) Writing a network forensics summary
A good summary translates packet artifacts into decision-ready intelligence.
Summary structure
- Case context: why packet analysis was initiated
- Data scope: capture source, timeframe, and limits
- Key observations: top suspicious behaviors with timestamps
- Correlation findings: what logs/endpoint data confirmed or disproved
- Assessment: likely benign, suspicious, or confirmed incident path
- Recommended actions: containment, deeper forensics, or closure criteria
One-page summary table
| Section | What to Include |
|---|---|
| Scope | Capture window, sensors, host focus |
| Findings | 3–5 evidence-backed observations |
| Confidence | Low/Medium/High with rationale |
| Impact | Potential business/operational effect |
| Actions | Immediate, short-term, and follow-up steps |
Keep language precise and avoid speculation beyond evidence.
9) Common mistakes in packet-based incident triage
- Jumping to conclusions based on one suspicious packet
- Ignoring timezone alignment across tools
- Modifying original PCAP instead of preserving source evidence
- Treating encrypted traffic as “no evidence” instead of using metadata + correlation
- Overlooking normal admin/scanner traffic context
- Failing to document filters and analysis steps used
- Reporting findings without confidence level or limitations
Quick anti-error checklist
- Time synced across packet, SIEM, and endpoint timelines
- Original evidence hashed and preserved
- Suspicious signals corroborated by at least one additional source
- Analyst notes include filters, pivots, and rationale
10) Wireshark IR checklist for recurring use
| Phase | Checklist Item | Done |
|---|---|---|
| Preparation | Case ID created and evidence handling plan documented | ☐ |
| Preservation | Original PCAP stored read-only with integrity hash | ☐ |
| Triage | Capture window and top talkers identified | ☐ |
| Protocol Review | DNS/HTTP/TLS/port behavior reviewed | ☐ |
| Correlation | Firewall, endpoint, and auth logs cross-checked | ☐ |
| Evidence | Key packet findings timestamped and documented | ☐ |
| Assessment | Confidence level and limitations stated | ☐ |
| Handoff | Summary and recommended actions delivered | ☐ |
When this workflow is followed consistently, Wireshark becomes more than a packet viewer. It becomes a reliable incident evidence engine that improves triage speed, confidence, and post-incident learning across security teams.
11) Escalation decision matrix for packet findings
Not every suspicious packet pattern should become a major incident. Use a decision matrix so escalation stays consistent.
| Signal Strength | Business Context | Recommended Action |
|---|---|---|
| Low (single weak indicator) | Low criticality asset | Continue monitoring and gather more context |
| Medium (multi-source suspicious indicators) | Standard production service | Open investigation case and assign analyst owner |
| High (clear malicious pattern + corroboration) | Critical service or sensitive data path | Escalate to incident response and containment immediately |
| High but uncertain scope | Mixed/unknown asset ownership | Escalate with limited containment and rapid ownership validation |
This avoids both overreaction and dangerous under-escalation.
12) 30-minute packet triage drill format
Teams get better when they practice speed and consistency under time pressure.
Drill structure
- 0–5 min: Confirm case context, capture scope, and key question
- 5–15 min: Run first-pass conversation/protocol analysis
- 15–25 min: Correlate one suspicious signal with endpoint/firewall/auth logs
- 25–30 min: Produce one-page summary and escalation decision
Drill scoring areas
| Area | What to Score |
|---|---|
| Evidence quality | Are observations timestamped and reproducible? |
| Correlation quality | Did analyst validate packet signal with another source? |
| Decision quality | Was escalation logic justified and consistent? |
| Communication quality | Was summary clear for responders and managers? |
Regular short drills make real incident packet triage faster and far more reliable.
Packet-analysis operations worksheet
| Workstream | Owner | First Action | Validation Signal |
|---|---|---|---|
| Evidence integrity | IR lead | Enforce hash + chain-of-custody on all PCAPs | No evidence handling gaps in case review |
| Triage consistency | SOC/IR analyst | Use standard question-to-evidence table per case | Faster and more reliable case decisions |
| Correlation quality | Detection/IR team | Require at least one secondary source correlation | Reduced false escalation based on packet-only signals |
| Reporting quality | Incident manager | Apply one-page summary format for each case | Leadership updates become clearer and faster |
Packet triage checklist
- Confirm capture time window and timezone normalization
- Identify top talkers and unusual external flows first
- Correlate suspicious packet signal with endpoint/firewall/auth logs
- Record confidence and limitations before escalation decision
Incident handoff pack for packet-driven cases
| Artifact | Minimum Content | Consumer |
|---|---|---|
| PCAP evidence sheet | Capture source, hash, timeframe, owner | Forensics + legal/compliance |
| Triage summary | Key packet findings and correlation results | Incident command |
| Escalation recommendation | Severity rationale + containment options | Response leadership |
| Follow-up tasks | Additional evidence or remediation actions | Technical owners |
Handoff quality checks
- Can another analyst reproduce the key finding path quickly?
- Are packet observations tied to clear operational actions?
- Are encrypted-traffic limitations documented honestly?
90-day packet triage capability plan
Days 1–30
- Standardize PCAP handling and summary templates
- Run weekly packet triage drills on sample scenarios
- Baseline analyst timing and confidence metrics
Days 31–60
- Improve cross-tool timeline correlation quality
- Refine escalation matrix based on drill outcomes
- Build reusable packet-analysis playbook snippets
Days 61–90
- Integrate packet-triage outputs into incident postmortems
- Track reduced decision time and false escalations
- Publish updated IR packet-analysis operating standard
| KPI | Why It Matters |
|---|---|
| Cases with complete evidence chain | Measures forensic reliability |
| Mean time to packet triage decision | Indicates response efficiency |
| Correlated multi-source confirmation rate | Reflects analysis quality |
| False escalation rate | Tracks decision accuracy |
Packet analysis creates the most value when evidence handling, triage logic, and escalation decisions are standardized and practiced as one repeatable IR capability.
PCAP readiness and governance (so captures are usable in real incidents)
Wireshark skills matter most when the organization can reliably produce the right captures, quickly, with appropriate privacy handling.
Capture policy basics
| Topic | Standard |
|---|---|
| Where to capture | Defined choke points (edge, DC, key VLANs) |
| When to capture | Triggered during incident windows + periodic baselines |
| Retention | Time-boxed retention aligned to policy and storage |
| Access | Least-privilege access to PCAPs and related keys |
| Privacy | Clear redaction/handling for sensitive data |
“Good PCAP” checklist
- Accurate timestamps (NTP synchronized).
- Interface and capture point documented.
- Known filtering decisions recorded (what was excluded and why).
- Associated artifacts linked: host logs, proxy logs, alerts, ticket ID.
Operational playbook integration
- Add a step in your IR runbook: “capture now” vs “capture on request.”
- Pre-stage tools/scripts for capture on critical hosts/segments.
- Define escalation: when packet analysis requires network engineering support.
Training and drills
- Quarterly drill: capture + analyze a benign scenario (e.g., DNS + TLS handshake) to validate toolchain.
- Post-drill review: identify missing telemetry, capture blind spots, and access bottlenecks.
This makes packet analysis a professional IR capability: repeatable capture, clear governance, and fast correlation to other evidence.